We may not have the course you’re looking for. If you enquire or give us a call on +36 18508731 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Imagine getting a message that looks like it came from a trusted friend, only to find out it was a trick. That's precisely the essence of IP Spoofing, a digital disguise used to trick networks and mask identities. Whether it’s for harmless testing or malicious attacks, this clever tactic plays a key role in Cyber Security.
This hidden deception can fuel powerful cyberattacks, from flooding servers with fake traffic to secretly intercepting private data. This blog breaks down the key aspects of IP Spoofing, spotlighting why it's such a threat in the online landscape. So read on and learn how to decode this deception before it strikes!
Table of Contents
1) What is IP Spoofing?
2) How IP Spoofing Works?
3) Types of IP Spoofing
4) How to Detect IP Spoofing?
5) How to Protect Against IP Spoofing
6) Common Uses of IP Spoofing
7) Real-world Examples of IP Spoofing
8) Conclusion
What is IP Spoofing?
Internet Protocol (IP) spoofing is a cyberattack where the attacker hides the real source of IP packets, making it hard to trace them. They accomplish this by changing the source IP address to pretend to be another computer or to disguise their identity. In a spoofed packet, the source IP shown is different from the actual one.
IP Spoofing is a Hacking method attackers use to carry out Distributed Denial of Service (DDoS) attacks and Man-in-the-middle attacks on devices or networks. In a DDoS attack, the aim is to flood the target with heavy traffic while hiding the attacker’s identity, making it harder to stop the attack.
How IP Spoofing Works?
Hackers exploit weaknesses in a system to launch an attack. They often use bots or infected computers, also known as zombies, to amplify the attack, resulting in severe damage. When data is sent between servers, it’s broken into packets. Each packet has a header with details like the sender’s IP address. Once packets reach their destination, they’re reassembled into the original data.
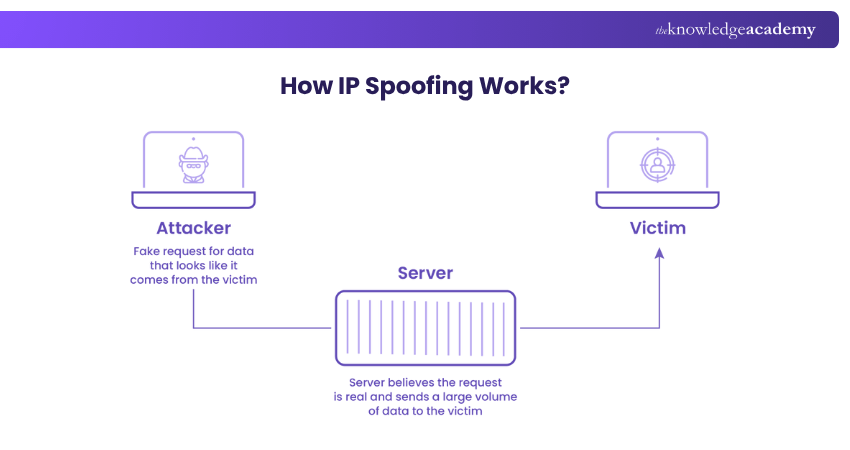
Most networks don’t check outgoing traffic closely, so fake information in packet headers can slip through without being noticed. To perform IP Spoofing, a Hacker usually needs the following:
1) Trusted Connection: Spoofs work best when two devices already trust each other. If one machine doesn’t need a login, it’s easier to exploit.
2) Controlled IP: The Hacker uses an address that can be ignored to avoid suspicion.
3) Coding Skills: They must know how to capture a packet and replace the real IP address
4) with a fake one.
IP Spoofing is fairly common because it requires only a basic level of technical skill to launch, but the potential benefits for attackers are substantial. Once the spoofing is done, these are the key points to remember:
1) Blocking the IP won’t work, since it points to an innocent device.
2) Without the real source address, you won’t know who to contact or how to fix it.
Soar above the benchmark of modern security our Certified Cloud Security Engineer Certification - Sign up now!
Types of IP Spoofing
There are four major types of IP Spoofing that can cause significant harm, ranging from loss of customer trust to serious legal complications. Let’s explore each type below:
1) Denial-of-service Attacks
In this type of attack, hackers use IP spoofing to flood a network or server with a massive volume of fake traffic. The system becomes so overwhelmed that it cannot process legitimate user requests, leading to downtime and service disruptions.
2) Data Interception
With spoofed IP addresses, Hackers can position themselves between two devices and secretly capture important information. This can include login details, credit card numbers, or private messages. Once stolen, this Data can be misused for fraud or identity theft.
3) Unauthorised Access
Attackers may disguise their IP address to trick a system into believing they are a trusted source. By bypassing security controls, they can gain entry into restricted networks or systems, giving them access to sensitive files, applications, or internal data.
4) Reputation Damage
IP Spoofing can also harm legitimate businesses or organisations. If attackers spoof a company’s IP address to launch attacks, it may look like the business is responsible. This can erode customer trust, harm brand reputation and even create legal or financial complications.
How to Detect IP Spoofing?
Detecting IP Spoofing is challenging because the attack happens at a low network level. That's where fake packets can look almost identical to real ones. However, these are some methods can help identify suspicious activity:
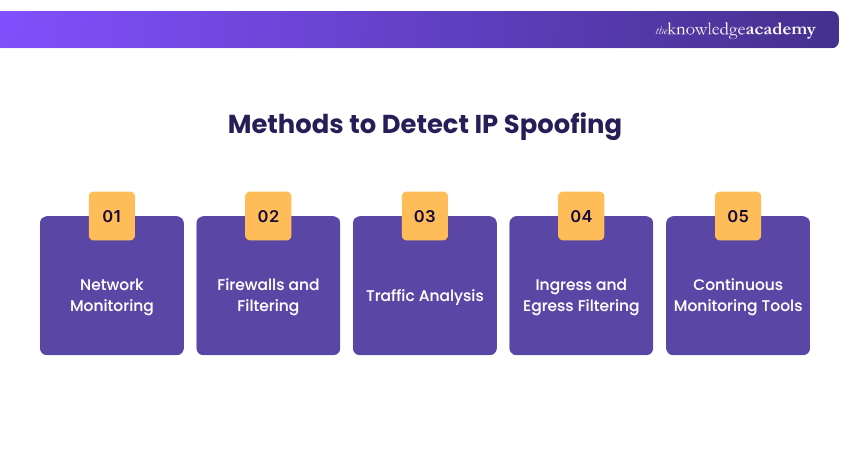
1) Network Monitoring: Keeping a close watch on network traffic is one of the most effective ways. IT Specialists often use Intrusion Detection Systems (IDS) or Intrusion Prevention Systems (IPS) to spot unusual traffic patterns. These patterns include sudden spike in requests and packets with mismatched source and destination details.
2) Firewalls and Filtering: Placing resources behind a firewall helps protect internal systems by blocking suspicious packets. Firewalls and routers can be configured to detect and reject packets that appear spoofed.
3) Traffic Analysis: Analysing packet headers and comparing them to expected behaviour can sometimes reveal spoofed traffic. For example, packets arriving from an IP address outside a normal geographic region or inconsistent with known communication patterns can be a red flag.
4) Ingress and Egress Filtering: Checking incoming and outgoing traffic helps detect inconsistencies. This makes it easier to identify packets that don’t match legitimate sources or attempt to exit the network with false IP addresses.
5) Continuous Monitoring Tools: Many organisations use automated monitoring systems that alert Administrators to unusual network behaviours, helping teams respond quickly.
Outsmarting Hackers has never been easier. Our comprehensive EC – Council Certification will show you how to stay one step ahead - Sign up now!
How to Protect Against IP Spoofing
While it’s not possible to completely stop spoofed packets, organisations can take several steps to reduce the risks and protect their networks. Here are the key steps:
1) Use strong authentication for remote access and avoid relying only on IP addresses.
2) Create an Access Control List (ACL) of trusted IP addresses.
3) Apply both ingress (incoming) and egress (outgoing) packet filtering.
4) Use Antivirus and security tools to detect suspicious network activity.
5) Encrypt IP traffic to prevent attackers from reading or copying addresses.
6) Keep all network software updated with the latest patches.
7) Continuously monitor network activity for unusual behaviour.
8) Configure firewalls and routers to reject spoofed packets. This includes private IPs coming from outside or internal traffic pretending to be from an external source.
Common Uses of IP Spoofing
Anyone with harmful intent might try to spoof an IP address, but it is mostly used for two main purposes.
1) Man-in-the-Middle (MITM): By pretending to be a trusted source, attackers can reroute traffic through their systems. This lets them read, change, or steal sensitive data before it reaches its intended destination.
2) Denial of Service (DoS): Hackers use fake IP addresses to flood a server with endless requests. Initially, it may involve only a few packets, but with amplification techniques, the attack can escalate to hundreds of gigabits per second. This can render the system completely unusable.
However, IP Spoofing isn’t always malicious. It can be used for legitimate reasons, too. For example, businesses may use it to simulate heavy website traffic before launching a new site. Security teams also use controlled IP Spoofing tests to find weaknesses in their systems and improve defences.
Real-world Examples of IP Spoofing
Here are three famous examples of IP Spoofing:
1) GitHub DDoS Attack (2018): In February 2018, GitHub suffered what was at the time the largest DDoS attack recorded. Attackers spoofed GitHub's IP addresses and exploited memcached servers to amplify incoming traffic by up to 50 times. This flooded GitHub with an astonishing 1.35 terabits per second. It causes about 10 minutes of downtime.
2) Europol’s Man-in-the-Middle Campaign (2015): Europol uncovered a man-in-the-middle attack across multiple European businesses in 2015. Hackers used IP Spoofing to intercept business–customer communications. They gained unauthorised access to corporate email accounts and enabled payment fraud.
3) Tsutomu Shimomura (1994): On December 25, 1994, Hacker Kevin Mitnick used IP Spoofing to attack Tsutomu Shimomura’s computer. He took advantage of the trust between Shimomura’s X terminal and its server by guessing TCP sequence numbers. Mitnick sent repeated SYN requests with fake IPs. This overloaded the computer’s memory. This technique is called SYN scanning.
Conclusion
IP Spoofing is like a digital masquerade; clever, deceptive and dangerous if left unchecked. By faking their online identity, attackers can launch powerful attacks or steal sensitive data. But with awareness, strong security practices and the right tools, you can spot the tricks and protect your network.
Harness the powerful blend of Cyber Security and Forensic brilliance in our Computer Hacking Forensic Investigator CHFI Certification – Sign up now!
Frequently Asked Questions
What is the Difference Between IP Spoofing and VPN?

IP Spoofing is a malicious technique where attackers fake an IP address to hide their identity or launch attacks. On the other hand, a VPN is a safe tool that masks your IP address to protect your privacy and secure your internet connection.
What are the Risks of IP Spoofing?

The biggest risks of IP Spoofing include Denial-of-service (DoS) attacks, unauthorised access to systems, data theft, and man-in-the-middle attacks. It can also damage a business's reputation if its IP addresses are spoofed and used in malicious activity.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various EC – Council Certification, including the Certified Ethical Hacker (CEH) Certification, Computer Hacking Forensic Investigator CHFI Certification and the Certified Application Security Engineer (CASE Java) Certification. These courses cater to different skill levels, providing comprehensive insights into Threat Intelligence Lifecycle.
Our IT Security & Data Protection Blogs cover a range of topics related to IP Spoofing, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Security and Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Computer Hacking Forensic Investigator CHFI Certification
Computer Hacking Forensic Investigator CHFI Certification
Mon 15th Jun 2026
Mon 24th Aug 2026
Mon 26th Oct 2026
Mon 30th Nov 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


