We may not have the course you’re looking for. If you enquire or give us a call on +852 2592 5349 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
In an era marked by increasing cyber threats and data breaches, the significance of Information Security Policies (ISP) cannot be overstated. As organisations increasingly depend on digital infrastructure to store and process sensitive data, strong methods are needed. However, by establishing Information Security Policies and implementing robust frameworks, organisations can mitigate risks, ensure compliance, and bolster trust among stakeholders in an ever-evolving threat landscape. To learn more about it, continue reading this blog.
Table of Contents
1) What is an Information Security Policy (ISP)?
2) Why is Information Security Policy (ISP) important?
3) Elements of an Information Security Policy (ISP)
a) Purpose
b) Target audience
c) Objectives of Information Security Policy
d) Policy on authority and access control
e) Categorisation of Data
f) Support and operations for data
g) Training on security awareness
h) Employee responsibilities and duties
i) Additional items in the Information Security Policy
4) Conclusion
What is an Information Security Policy? (ISP)
An Information Security Policy (ISP) is a set of guidelines and procedures that ensure the confidentiality, integrity, and availability of an organisation's data and information systems. It covers measures and protocol that need to be adhered to for minimalising the risks. The Information Security Policy (ISP) is meant to ensure that all sensitive data are safe from any unauthorised access, use, disclosure, alteration, or destruction.
Why is Information Security Policy Important?
Information Security Policies provide a structure consisting of guidelines so that employees can manage risks related to security effectively, fulfilling legal and regulation needs. It promotes a culture of security consciousness among employees toward the assets and reputation of the organisation. Information Security Policies, with clear guidelines and standards, mitigates the upcoming potential threats and vulnerabilities, thus improving and building trustful confidence of stakeholders.
Elements of an Information Security Policy
The elements of an Information Security Policy are the foundation that outlines how to protect sensitive data and ensure the integrity of information systems within organisations. Let us look at each element in detail:
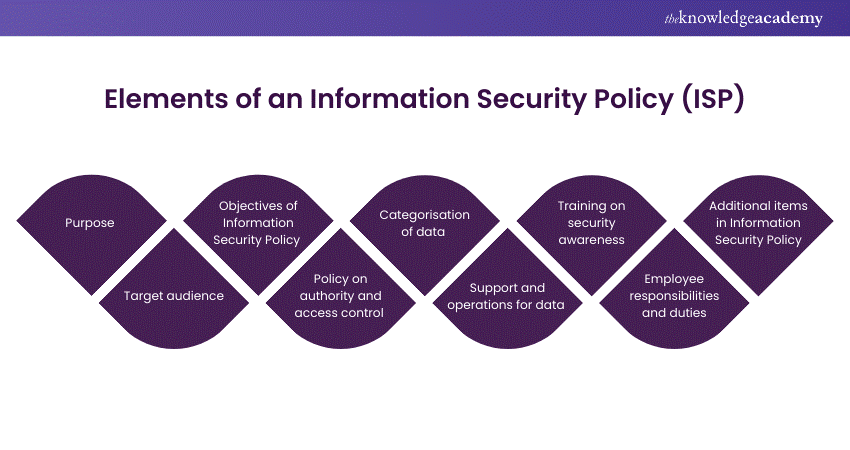
1) Purpose
Information security policy ensures that organisations on the safekeeping of sensitive information. The section focuses on the ability to detect and prevent security breaches from third-party vendors, misuse of networks, and data and access to the system not authorised by the organisation.
Ensuring adherence to ethical, legal, and regulatory requirements preserves the organisation's reputation. The involvement of a Deputy Chief Information Security Officer is key to facilitating the organisation's ability to effectively respond to inquiries and complaints regarding non-compliance.
2) Target audience
Information Security Policies (ISP) are not limited to a select few but are intended for all stakeholders interacting with the organisation's information resources. From executives and managers to IT staff and end-users, everyone has a role to play in upholding the organisation's security standards.
3) Objectives of Information Security Policy
An effective Information Security Policy sets clear objectives to guide security efforts. This may include:
a) Protecting sensitive information from unauthorised access.
b) Preventing security breaches and data breaches.
c) Ensuring compliance with applicable laws, regulations and industry standards.
d) Promoting a culture of security awareness and accountability.
Learn cybersecurity management with our Chief Information Security Officer Course- register today!
4) Policy on authority and access control
This aspect brings in the question of who actually is in a position to determine the kind of data that should be shared, and the type that should not. It outlines roles and criteria for rights and responsibilities of persons authorised to access the organisation's information systems and procedures pertaining to allocation, modification, and verification of access rights.
5) Categorisation of data
Data classification is essential for prioritising security measures based on the sensitivity and criticality of the information. This section defines the criteria for classifying data and specifies the security controls required for each category.
6) Support and operations for data
After the data is categorised, the technical and operational aspects are addressed. It covers the procedures of managing and protecting data. From data backup and recovery procedures to encryption standards, it checks whether data protection measures are in place or not.
7) Training on security awareness
Security awareness training is crucial for educating employees about potential security threats. It emphasises requirements for training programs and methods for assessing their effectiveness, enabling employees to identify and reduce risks.
Learn best practices to mitigate security risks and challenges with our Information Systems Security Management Course- join today!
8) Employee responsibilities and duties
Employees play a vital role in maintaining information security. This element outlines their responsibilities, emphasising their role in protecting sensitive information and adhering to security policies and procedures.
9) Additional items in Information Security Policy
Depending on the organisation's specific needs and industry requirements, additional topics may be included in the Information Security Policy (ISP), such as:
a) Remote access policies
b) Mobile device security
c) Incident response and reporting procedures
d) Third-party security requirements
e) Compliance with privacy regulations
Conclusion
Information Security Policies are essential for protecting an organisation's valuable assets and maintaining trust with stakeholders. Organisations can minimise and prevent risks by defining clear guidelines and standards for information security. A Virtual Chief Information Security Officer (CISO) can help in creating and implementing these policies, ensuring they are aligned with industry standards and best practices. Moreover, creating and implementing Information Security Policies have become a step towards safeguarding against evolving cyber threats in today's digital landscape.
Gain in-depth knowledge about how to report IT performance with our CISA Certified Information Systems Auditor Course- join today!
Frequently Asked Questions
What is one of the major challenges of Information Security Policies?

The greatest challenge posed by Information Security Policies is compliance and adherence at all levels within an organisation, including relevance and effectiveness in changing threats and technologies.
What is the key function of an Information Security Policy?

The main aim of having an Information Security Policy (ISP) is to provide a comprehensive framework for ensuring the protection of information assets in an organisation, including the confidentiality, integrity, and availability of those assets.
What are the other resources and offers provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is the Knowledge Pass, and how does it work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are related IT Security & Data Protection Courses and blogs provided by The Knowledge Academy?

The Knowledge Academy offers various CISM Training, including CISM Certified Information Security Manager Course. This course caters to different skill levels, providing comprehensive insights into Best CISM Books.
Our IT Security & Data Protection Blogs cover a range of topics related to CISM, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

The Knowledge Academy is a world-leading provider of professional training courses, offering globally recognised qualifications across a wide range of subjects. With expert trainers, up-to-date course material, and flexible learning options, we aim to empower professionals and organisations to achieve their goals through continuous learning.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 CISA Certified Information Systems Auditor
CISA Certified Information Systems Auditor
Mon 15th Jun 2026
Mon 14th Sep 2026
Mon 14th Dec 2026





 Top Rated Course
Top Rated Course








 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


