We may not have the course you’re looking for. If you enquire or give us a call on +30 2111995372 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Not all Cyberattacks are loud and obvious. In many instances, the attackers silently slip into networks and reroute data like digital pickpockets. ARP Spoofing is one such silent threat. It manipulates network communications at the data-link level, allowing Hackers to intercept, modify or redirect traffic without detection.
So how do you catch this digital imposter posing as a trusted connection, hijacking conversations between devices? This blog has the answer for you. Here we explore how ARP Spoofing works, its dangers and the smart defences every network should have to stay protected. So read on and stay ahead of one of the internet’s sneakiest threats!
Table of Contents
1) What is ARP?
2) What is ARP Spoofing?
3) Characteristics of ARP Spoofing Attacks
4) How Does ARP Spoofing Work?
5) Types of ARP Spoofing Attacks
6) Detecting, Preventing and Defending Against ARP Spoofing
7) Cyber Security Impact of ARP Spoofing Attacks
8) Best Practices for Preventing ARP Spoofing Attacks
9) Recommended Tools for ARP Spoofing Protection
10) Conclusion
What is ARP?
The Address Resolution Protocol (ARP) is a communication protocol used in computer networks to map an Internet Protocol (IP) address to a physical machine address, known as a Media Access Control (MAC) address. When a device wants to communicate with another on the same local network, it uses ARP to find out the corresponding MAC address associated with the destination IP address. This allows data packets to reach the correct hardware device on the network.
When a device sends an ARP request, all devices on the local network receive it, but only the device with the matching IP address responds with its MAC address. This information is then stored temporarily in an ARP cache for faster access in future communications. ARP plays a vital role in enabling seamless data transmission within local area networks (LANs).
What is ARP Spoofing?
ARP Spoofing refers to a cyberattack in which the Hacker sends forged Address Resolution Protocol (ARP) messages across a LAN. This deceptive tactic links the attacker’s MAC address to the IP address of a trusted device or server, thus allowing them to receive data meant for that system.
Once the attacker has rerouted the traffic, they can intercept or block data in transit. Such attacks are limited to networks that use the Address Resolution Protocol. This makes LAN environments particularly vulnerable if not properly secured.
Characteristics of ARP Spoofing Attacks
Here are the key characteristics of ARP Spoofing attacks:
1) Exploitation of ARP’s Trust Mechanism: ARP operates on implicit trust, as it does not verify the authenticity of requests or responses. This makes networks naturally susceptible to deception.
2) Real-time Data Interception: Attackers can manipulate network communication instantly without prior access. This helps them exploit device trust to redirect data traffic.
3) Network Disruption Potential: Continuous spoofing can overwhelm or destabilise systems. They can potentially cause widespread failures across connected networks.
Recognising these traits is essential to effectively detect and prevent ARP Spoofing attacks.
Purpose of an ARP Spoof Attack
The main aim of an ARP spoofing attack is to poison the Address Resolution Protocol tables on devices in a local network so the attacker can intercept, redirect or disrupt traffic. Typical outcomes include:
1) Eavesdropping: This is where attackers secretly capture sensitive data like passwords or financial details.
2) Data Modification: This is where the attacker alters or injects malicious code into packets during transit, compromising data integrity.
3) Denial-of-Service (DoS): In these conditions, spoofed responses overload or misroute traffic, causing significant network delays or complete service disruptions.
How Does ARP Spoofing Work?
ARP Spoofing attacks generally follow a predictable sequence. The steps to an ARP Spoofing attack typically include the following:
1) The attackers configure an ARP-spoofing tool on the target’s IP subnet.
2) They scan the subnet to identify active hosts and collect their IP and MAC addresses.
3) They select a victim and craft forged ARP packets that pair the victim’s IP with the attacker’s MAC.
4) They broadcast the spoofed ARP replies across the LAN so other devices cache the false mappings.
5) They intercept redirected traffic destined for the victim’s IP, then exfiltrate data or launch further attacks.
In a world of evolving digital threats, knowledge is your firewall. Boost your defences with our Cyber Security Training - Sign up now!
Types of ARP Spoofing Attacks
Recognising the different forms of ARP Spoofing can help Network Administrators and security teams defend infrastructure more effectively. Common variants of these attacks include:
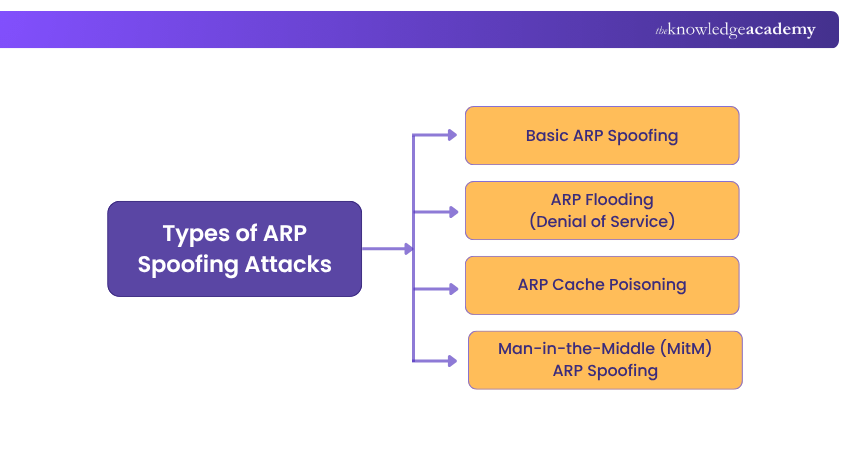
1) Basic ARP Spoofing
An attacker sends forged ARP replies, so a device associates the attacker’s MAC address with a legitimate IP (for example, a gateway). The attacker then captures or alters traffic destined for that IP without the victim noticing.
2) ARP Flooding (Denial of Service)
The attacker overwhelms the network with a large number of fake ARP replies, corrupting ARP tables and preventing devices from maintaining correct mappings. The result can be partial network outage or degraded connectivity.
3) ARP Cache Poisoning
The attacker sends unsolicited, forged ARP replies to overwrite legitimate IP→MAC entries in devices’ ARP caches. Poisoned entries persist until cleared or the device reboots. This allows traffic to be redirected to the attacker or another malicious host for disruption or further exploitation.
4) Man-in-the-Middle (MitM) ARP Spoofing
The attacker positions themselves between two communicating hosts by forging ARP responses. Each host believes it is talking directly to the other. This enables interception or modification of traffic.
Detecting, Preventing and Defending Against ARP Spoofing
To protect your networks from ARP Spoofing attacks, here are some proactive strategies you can implement:

1) Deploy Packet Filtering: Deploy filters to inspect data packets as they traverse the network. These filters can block packets containing conflicting or suspicious source address information. This prevents external packets from appearing as if they originated within the network.
2) Minimise Trust Relationships: Reduce your reliance on IP-based trust authentication because such configurations make networks more susceptible to spoofing. Implement strong authentication protocols instead of simple IP verification.
3) Use ARP Spoofing Detection Software: Use specialised tools that analyse network traffic to detect irregularities in ARP messages. These programs validate the data before transmission and block traffic identified as spoofed.
4) Adopt Cryptographic Network Protocols: Use secure communication protocols such as TLS, SSH and HTTPS to encrypt transmitted data and authenticate its source. This prevents attackers from intercepting information even if ARP Spoofing occurs.
Catch the fraud before it catches you. Sign up for our Fraud Analytics Training now and uncover fraud with the power of analytics!
Cyber Security Impact of ARP Spoofing Attacks
The consequences of ARP Spoofing extend far beyond network disruption. They pose significant risks to both individuals and organisations. Once compromised, the resulting damage can be difficult to recover from completely. Here are its impacts:
1) Data Theft: Attackers can steal sensitive credentials, private communications, financial details etc., particularly on unencrypted networks. Such breaches expose confidential information, leading to reputational harm and potential legal repercussions.
2) Network Disruption: Manipulating ARP tables or rerouting traffic can severely degrade network performance. This can cause outages and trigger denial-of-service conditions, resulting in operational downtime and productivity loss.
3) Malware Distribution: By injecting malicious code into intercepted traffic, attackers can spread malware across connected systems. This can lead to data corruption, large-scale infections and further security vulnerabilities within the network.
Best Practices for Preventing ARP Spoofing Attacks
Here are some best practices to consider:
1) Enable Dynamic ARP Inspection (DAI): Use DAI on network switches to verify ARP packets against trusted IP-MAC mappings. This blocks malicious packets before they reach devices.
2) Monitor Network Traffic: Continuously track ARP activity and traffic patterns to identify unusual behaviour or mapping changes that may indicate spoofing.
3) Use Encryption Protocols: Protect communications with HTTPS, SSH and VPNs to ensure intercepted data remains unreadable without decryption keys.
Recommended Tools for ARP Spoofing Protection
There are plenty of tools that can help identify potential ARP-related issues before they cause harm. Here are some of the widely used solutions for ARP Spoofing:
1) Arpwatch: This is a Linux-based tool that monitors Ethernet activity and tracks changes in IP and MAC addresses. Daily log reviews and timestamps help pinpoint when the suspicious activity occurs.
2) ARP-GUARD: This provides a visual map of your network, showing switches and routers. It learns about connected devices and allows administrators to create rules to securely manage new connections.
3) XArp: This tool detects ARP attacks that bypass firewalls. It issues real-time alerts and offers detailed diagnostics to guide response actions.
4) Wireshark: It offers graphical network analysis and displays all active devices and packet data. Though powerful, it requires advanced knowledge to use effectively.
5) Packet Filtering: This is a firewall method that controls network access by allowing or blocking packets based on source/destination IPs, ports, and protocols.
6) Static ARP Entries: These permanently map IP and MAC addresses to prevent unauthorised devices from impersonating trusted systems.
Conclusion
ARP Spoofing may lurk around unseen, but understanding its tactics is the first step to outsmarting it. With the right tools and persistent vigilance, your networks can stay resilient against such invisible intrusions. After all, in the digital battleground of trust and deception, awareness remains the strongest firewall every organisation can build.
Learn to detect, respond, and recover from breaches with confidence. Our Incident Response Training will show you how - register now!
Frequently Asked Questions
What Happens When a Router Receives an ARP Request?

When a router receives an ARP request, it checks whether the requested IP address matches any of its own interfaces. If it does, the router replies with its MAC address. If not, it forwards the request to the appropriate network segment or ignores it, depending on configuration and routing rules.
How do You Know if You have ARP Poisoning?

Signs of ARP poisoning include:
1) Network slowdowns
2) Frequent disconnections
3) Duplicate IP address alerts
4) Mismatched MAC addresses in your ARP table
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including Certified Cyber Security Professional (CCS-PRO) Course, Introduction to System and Network Security Course and the Certified Artificial Intelligence (AI) For Cyber Security Professionals Training. These courses cater to different skill levels, providing comprehensive insights into Incident Response.
Our IT Security & Data Protection Blogs cover a range of topics related to ARP Spoofing, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Cyber Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Introduction to System and Network Security
Introduction to System and Network Security
Fri 28th Aug 2026
Fri 13th Nov 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


