We may not have the course you’re looking for. If you enquire or give us a call on +33 805638382 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

The rise of advanced cyber threats requires organisations to establish effective security monitoring systems. What is SIEM and why do organisations rely on it to protect their systems and data? Let us investigate the operation of this solution because it serves as an essential component of current cybersecurity methods.
Table of Contents
1) What is a SIEM?
2) How Does SIEM Work?
3) What are the Key Features of a SIEM Solution?
4) Benefits of SIEM
5) SIEM Use Cases
6) Best Practices for Implementing SIEM
7) Conclusion
What is a SIEM?
A SIEM solution collects security data from applications and devices and servers and users to analyse the data in real time, which creates a complete security overview for organisations. This enables security teams to detect and investigate incidents while responding to them in a more efficient manner.
How Does SIEM Work?
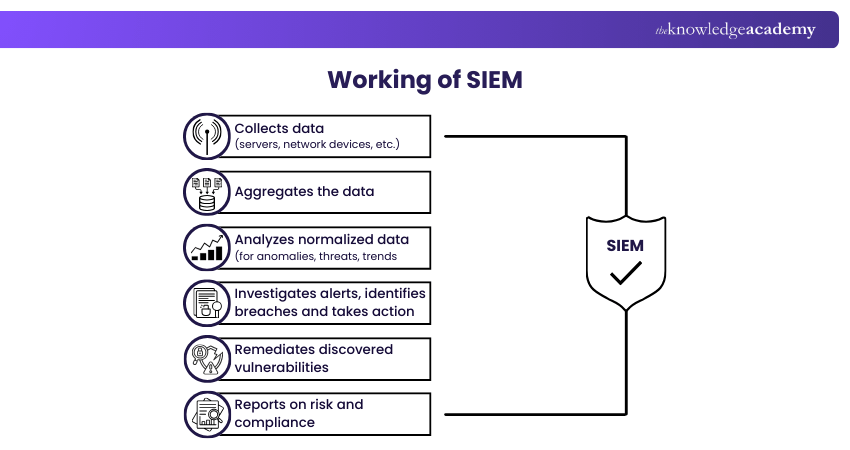
The system collects and stores all log data together with event data from different systems and applications and security tools into one unified platform. The system uses real-time data analysis to find both abnormal behavior and security risks within the information system.
The solution identifies different types of events through its event categorisation system which includes login attempts and access changes and then uses correlation rules to discover patterns. Security teams use this method to identify advanced attacks which single security events cannot detect.
SIEM stores all log data for two main purposes which include investigative work and compliance documentation. The system provides teams with both current system status information and past incident details which helps them handle incidents effectively.
Cyber risks are real, so make sure your readiness is too. Sign up for our Cyber Security Risk Management Course now!
What are the Key Features of a SIEM Solution?
A modern SIEM solution includes features that enhance visibility, improve threat detection, and support efficient incident response, such as:
a) Log Management and Data Aggregation: Logs collected from different sources are centralised in order to offer a collective view of the IT environment.
b) Security Monitoring and Alerting: It consistently tracks activity and provides alerts in real-time regarding any unusual occurrences.
c) Threat Intelligence and Correlation: Correlating threat intelligence against event data and identifying patterns of malicious activity.
d) Incident Response and Investigation: Mitigates root causes in a quick time, and at the same time analyses behaviour as far as security is concerned.
e) Data Retention for Compliance and Reporting: It stores security data for both long and short terms and will generate reports in order to meet both regulatory and audit requirements.
Benefits of SIEM
From real-time threat detection to Improved SOC Efficiency, SIEM brings many benefits to the table. Let's explore them:
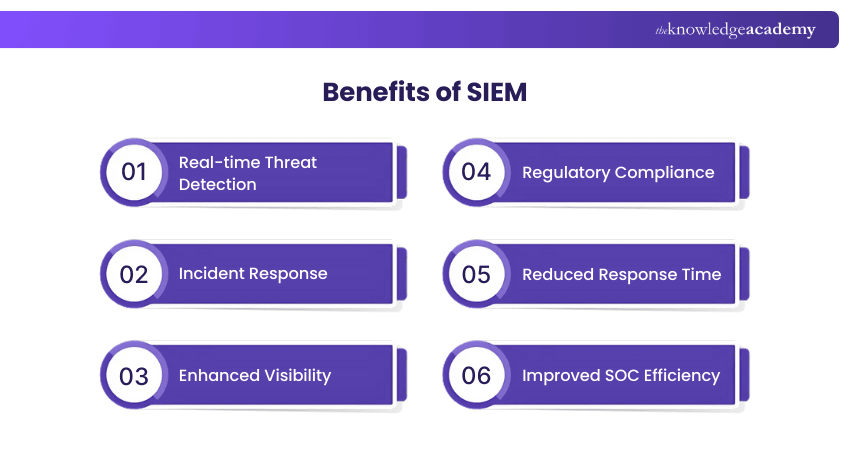
1) Real-time Threat Detection
Attackers often move across apps, devices, and users, making them hard to spot. SIEM solutions analyse and link data from across the environment, helping SOCs detect and respond to hidden, multidomain threats faster.
2) Incident Response
Instead of digging through separate logs, Analysts can see all important data in one place, which helps them focus on the most serious threats. SIEM also shows clear event timelines, user activity, and reports to find the root cause of an attack. When connected with SOAR tools, SIEM can automate tasks like blocking suspicious IPs or isolating devices.
3) Enhanced Visibility
With people working remotely and systems spread across different clouds, attackers can have more ways to target organisations. Monitoring all these entry points manually is nearly impossible, but SIEM makes it easier by collecting data and insights in one place.
4) Regulatory Compliance
SIEM helps organisations stay compliant with real-time audits and automated reporting. This significantly reduces the risk of fines or penalties and protects the organisation’s reputation with customers and regulators.
5) Reduced Response Time
With improved collaboration and thorough investigations, security teams can respond to security threats more effectively. Many SIEM platforms also include AI automation to handle routine incidents, freeing humans to focus on complex challenges.
6) Improved SOC Efficiency
SIEM reduces manual work in SOCs. Central dashboards and event correlation highlight serious incidents quickly, while reports and SOAR integration improve teamwork and speed up response efforts.
Embrace cyber awareness and outsmart cyber threats at every turn. Sign for our Cyber Security Awareness Training now!
SIEM Use Cases
Security teams use SIEM solutions for multiple purposes, which they use to improve their protection capabilities and incident response operations. Some of these cases are listed below:
a) Threat Detection and Response – SIEM technology enables security teams to identify and counteract advanced threats, which include insider threats and multi‑domain intrusions.
b) Compliance Management – The system automatically gathers data, which enables it to create customised compliance reports that meet regulatory standards.
c) Forensic Analysis – SIEM delivers comprehensive reporting and analytical tools that enable teams to track attack movements while determining all affected assets during their investigation process.
Best Practices for Implementing SIEM
Implementing a Security Information and Event Management (SIEM) system is a crucial step in enhancing your organisation's Cyber Security posture. To ensure a successful implementation, consider the following best practices:
1) Plan Thoroughly
Define clear goals and priorities for your SIEM deployment, considering data, compliance needs, and future security growth.
2) Outline Use Cases and Security Roadmap
Identify key security objectives and ensure you feed complete, accurate data into SIEM to make it effective.
3) Maintain and Continuously Improve
Treat SIEM as an evolving tool by regularly reviewing and adjusting its configurations to match changing security needs.
4) Fine-tune Alerts
Set precise alert criteria and continuously refine settings to focus on real threats and reduce noise.
5) Invest in Skilled Staff
Ensure trained personnel are in place to manage, optimise, and adapt your SIEM effectively over time.
Conclusion
Understanding What is SIEM, is key to detecting threats and responding effectively. Cybersecurity risks can be managed by organisations that implement core features together with best practices. The blog demonstrated to readers its value for system protection.
Boost your skills and protect digital assets with Cyber Security Training - Register today for expert guidance!
Frequently Asked Questions
What is the Difference Between SIEM and SOAR?

The Security Information and Event Management system collects security data which it analyses to identify threats. The Security Operations Automation and Response platform automates its response systems and operational processes together with its incident management system to handle alerts with increased efficiency.
What is a SIEM vs SOC?

A SIEM is a security technology which collects and processes security event data to detect potential threats. A SOC is the team of professionals who use tools like SIEM to monitor, investigate, and respond to security incidents.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including the Cyber Security Awareness, Digital Forensics Training, and Malware Analysis Training. These courses cater to different skill levels, providing comprehensive insights into Incident Response.
Our IT Security & Data Protection Blogs cover a range of topics related to SIEM, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 24th Apr 2026
Fri 24th Jul 2026
Fri 9th Oct 2026







 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


