We may not have the course you’re looking for. If you enquire or give us a call on 0800 446148 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
You check your inbox between meetings. A message looks urgent, familiar, and perfectly timed. It asks for a quick action, nothing unusual. Many people click without thinking because it feels routine. That simple moment of trust is exactly what Social Engineering attackers rely on every day.
Understanding What is Social Engineering helps you spot these situations early. This blog explains common tactics attackers use and shares practical tips to help you protect your data, money, and peace of mind.
Table of Contents
1) Social Engineering Definition
2) How Does Social Engineering Work?
3) Various Types of Social Engineering Attacks
4) What Does a Social Engineering Attack Look Like?
5) Examples of Social Engineering Attacks
6) Ways to Protect Yourself from Social Engineering
7) Tips to Remember
8) Conclusion
Social Engineering Definition
Social Engineering involves harmful tactics that exploit human interactions by using psychological methods to trick individuals into revealing sensitive information or making security mistakes. Attackers typically start by researching their targets to find weaknesses, then gain their trust to persuade them into breaking security rules, such as sharing confidential details or granting access to protected resources.
Common Social Engineering techniques include phishing emails, pretexting, baiting, and tailgating. Understanding What is Social Engineering helps explain how these methods exploit urgency, fear, and trust, often leading to data breaches, financial losses, and serious damage to an organisation’s reputation.
How Does Social Engineering Work?
The success of most attacks relies on direct interaction between attackers and their targets. Social Engineering attackers do not use brute force; instead, they rely on psychological tactics to manipulate victims into compromising themselves.
The Social Engineering attack cycle provides a structured way to deceive individuals and typically includes:
1) Preparation: Collecting background information about the target or group
2) Infiltration: Establishing a connection and building trust
3) Exploitation: Using trust and known vulnerabilities to carry out the attack
4) Disengagement: Withdrawing after the attacker achieves their objective
This process may occur through a single email or extended interactions. By exploiting trust and posing as IT support, attackers trick victims into sharing data, installing Malware, resetting passwords, or granting system access.
Various Types of Social Engineering Attacks
Social Engineering attacks come in many forms, each designed to exploit human vulnerabilities. Let’s understand these types to recognise and defend against these deceptive Social Engineering tactics:
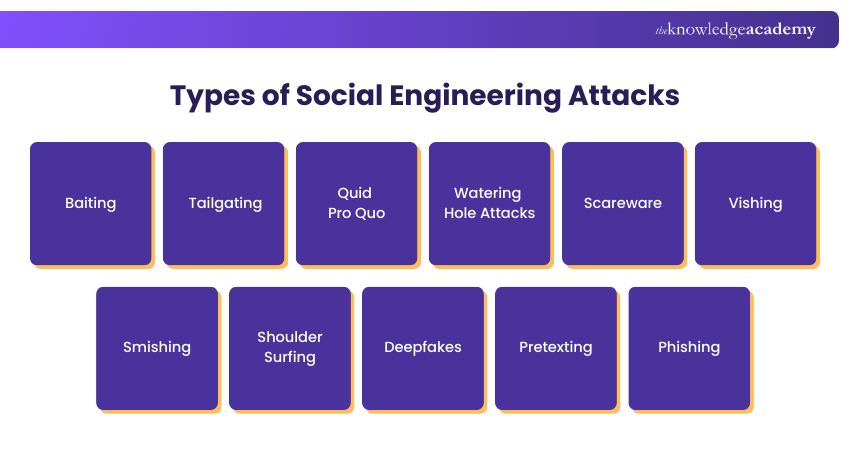
1) Baiting
Baiting deceives victims with enticing offers or free products enticing them to either divulge sensitive information or download malware. Examples of baiting include scams such as the "Nigerian Prince" scam and newer methods that involved infected downloads, and leaving USB drives in public for the unsuspecting to plug into their devices.
2) Tailgating
Tailgating, also known as "piggybacking," refers to the act of an individual without authorisation closely following someone into a restricted area. This could involve physically following an employee through an unsecured door. Alternatively, it could be a technological manoeuvre, like hacking into a computer that remains logged in.
3) Quid Pro Quo
In a Quid Pro Quo scheme, attackers give something desirable to obtain sensitive information. Instances consist of false competition winnings or loyalty bonuses offering presents in exchange for personal information.
4) Watering Hole Attacks
Hackers carry out a watering hole attack by inserting harmful code into a trusted website that is often visited by their desired victims. This could lead to various outcomes, ranging from stolen login information to drive-by ransomware installations.
5) Scareware
Fear is employed by scareware to control its victims. Frequently, it presents itself as a phoney law enforcement notification alleging the user of committing a crime or a tech support alert regarding malware. Victims are deceived into disclosing information or installing malicious software.
6) Vishing
Vishing (voice phishing) involves phone calls from scammers posing as banks, tech support or government officials. They often create panic to pressure victims into sharing personal details.
7) Smishing
Smishing uses text messages to lure people into clicking on malicious links or providing confidential information. These messages may appear to come from delivery services, banks or even friends.
8) Shoulder Surfing
This old-school technique involves physically observing someone to steal information. Whether it’s peeking over a shoulder at an ATM or glancing at a phone screen on the train, attackers look for passwords, PINs or other private data in public places.
9) Deepfakes
Deepfakes use AI to create highly realistic fake videos or audio. In the wrong hands, they can impersonate CEOs, political leaders or even colleagues to spread false information or authorise fraudulent transactions. As the technology improves, spotting a deepfake becomes harder, making it a serious threat.
10) Pretexting
Pretexting is the act of creating a believable false story in order to build a rapport with a victim and persuade them to share sensitive information. This process requires extensive research and careful planning to seem credible.
11) Phishing
Phishing is a method that uses bogus emails or messages designed to entice victims to disclose personal data or click on links that are known to be malicious. Phishing messages often masquerade as familiar organisations, like banks or online services, so victims will type their credentials on bogus websites.
Become a malware analysis expert with our Malware Analysis Training – Sign up now!
What Does a Social Engineering Attack Look Like?
Social Engineering attacks often appear as trusted, everyday communication. By exploiting familiarity, urgency, or emotion, attackers manipulate people into unsafe actions, as seen in the common tactics below.
1) Email from a Friend
In this attack, criminals hijack a person’s email or social account to message their contacts. Because it appears to come from a trusted friend, victims click links or attachments that install malware and spread the attack further.
2) Email from Another Trusted Source
These attacks impersonate trusted organisations such as banks, employers, or charities. Often called phishing, they create urgency or offer rewards to trick victims into sharing login details, financial data, or personal information.
3) Baiting Scenarios
Baiting attacks tempt victims with free downloads, discounts, or exclusive deals. Once the bait is taken, malware may be installed, money lost, or sensitive data exposed without the victim realising the risk.
4) Response to a Question You Never Had
In this scenario, attackers reply to a support request the victim never made. By posing as a customer or technical support, they exploit confusion to obtain login details or remote access, gaining control of the system.
5) Creating Distrust
This attack spreads doubt, conflict, or fear by manipulating private messages or information. In some cases, the stolen material is used for blackmail or extortion to force compliance or payment.
Learn to detect and prevent fraud using data-driven techniques and risk indicators. Join our Fraud Analytics Training now!
Examples of Social Engineering Attacks
Social Engineering Attacks are some of the most deceptive and dangerous tactics used in cybercrime. Rather than exploiting technical vulnerabilities, these attacks manipulate human psychology to gain access to confidential data or systems. Let’s explore some of the most infamous examples and attack vectors to better understand how they work and why they’re so effective.
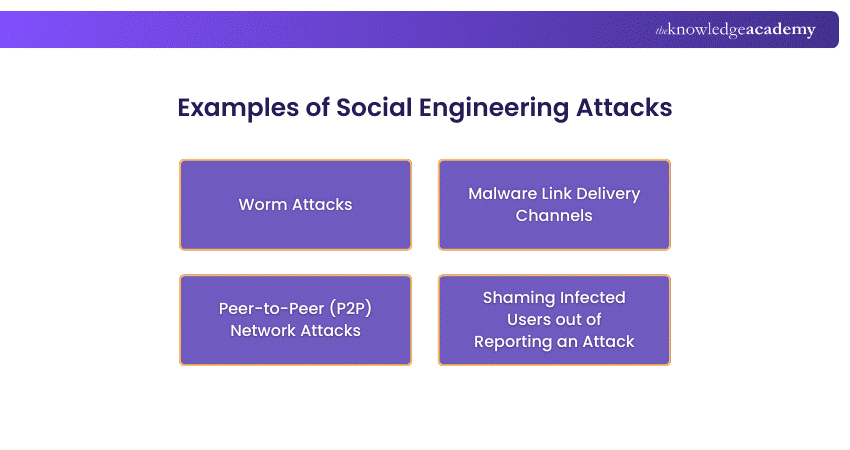
1) Worm Attacks
Worms are self-replicating malware that spread quickly across systems and networks without any user involvement. They often disguise themselves as harmless files or tempting messages to avoid detection. This allows them to move unnoticed between devices and users.
Once activated, worms can cause widespread damage within minutes by copying themselves, consuming system resources, and opening pathways for further attacks across connected devices. In many cases, they also slow down networks or disrupt critical services across entire organisations.
The Love Letter Worm
The Love Letter Worm (ILOVEYOU) spread in 2000 through an email titled “I LOVE YOU” that contained a deceptive attachment. By exploiting curiosity and emotional appeal, it overwrote important files and forwarded itself to contacts in the victim’s address book. It became one of the earliest and most damaging examples of large-scale Social Engineering attacks.
The Mydoom Email Worm
The Mydoom Email Worm emerged in 2004 and spread rapidly by posing as a bounced message or system error. Once opened, it replicated through email, created remote-access backdoors, and launched denial-of-service attacks, highlighting the impact of Social Engineering at scale.
The Swen Worm
The Swen Worm disguised itself as a Microsoft Windows update using a fake installation wizard. Once installed, it harvested email addresses and spread further, demonstrating how fake credibility can create serious security risks.
2) Malware Link Delivery Channels
Cybercriminals use multiple channels to deliver malicious links, including emails, social media posts, instant messaging apps, online ads, chat rooms, and SMS messages. These links often use eye-catching language such as free offers, urgent warnings, or trending news to encourage users to click without thinking.
Once clicked, the link may install spyware, ransomware, or backdoor tools, sometimes bypassing antivirus filters. These attacks are especially dangerous because the messages often look authentic, closely imitating communications from trusted banks, companies, or popular websites.
3) Peer-to-Peer (P2P) Network Attacks
P2P networks allow users to share files directly, but this convenience comes with significant risk. Attackers often hide malicious code inside popular music, movies, or software downloads, tricking users into installing malware unknowingly. These files are often named to look attractive or legitimate, increasing the chances of being downloaded.
Because P2P networks lack central control or filtering, infected files can appear genuine and spread easily. This makes it easier for attackers to distribute malware and gain control of users’ devices. As a result, users may compromise their security without realising it until significant damage has already occurred.
4) Shaming Infected Users out of Reporting an Attack
One of the darker tactics in the Social Engineering playbook is psychological manipulation that keeps victims silent. Attackers often design Social Engineering malware, particularly those involving adult content or illegal downloads in a way that makes the user feel embarrassed or guilty. Victims might fear being judged, disciplined, or even prosecuted if they come forward.
As a result, infections go unreported and untreated, giving the malware more time to spread and collect data. It’s a cruel but effective method that exploits shame and fear to maintain secrecy. This delay significantly increases the overall damage and recovery time for affected individuals and organisations.
Advance your career with the Certified Cyber Security Professional (CCS-PRO) Course – Register Today!
Ways to Protect Yourself from Social Engineering
Protecting yourself from Social Engineering requires practical security habits. Since these attacks exploit human behaviour, the following Social Engineering strategies help reduce exposure and limit damage.
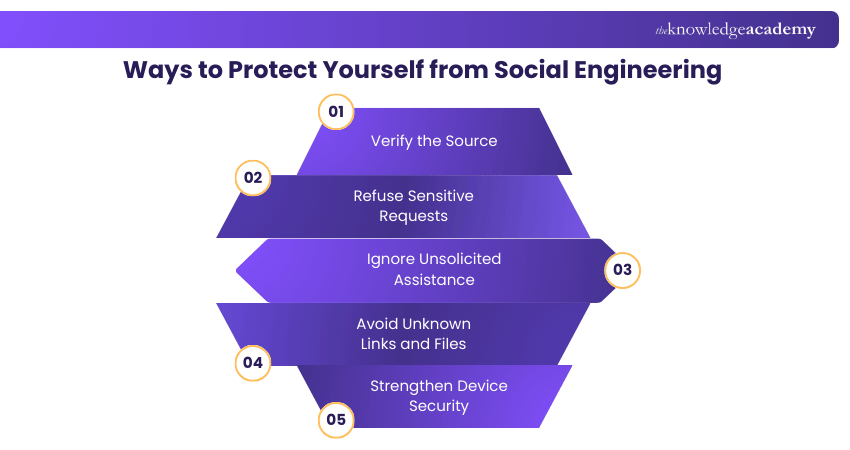
1) Verify the Source: Confirm the identity of senders using official websites or verified contact details before responding.
2) Refuse Sensitive Requests: Delete messages asking for passwords, PINs, or financial details, as legitimate organisations never request this information.
3) Ignore Unsolicited Assistance: Avoid offers of help or donation requests that you did not initiate or expect.
4) Avoid Unknown Links and Files: Do not interact with unexpected links or attachments sent via email or messages.
5) Strengthen Device Security: Use antivirus tools, enable spam filters, and keep operating systems and applications up to date.
Tips to Remember
These simple reminders help you recognise warning signs and respond safely in everyday situations.
1) Pause Before Acting: Urgent or emotional messages are designed to push quick decisions. Take time to assess them.
2) Find Websites Independently: Use a search engine instead of clicking embedded links to reach official sites.
3) Assume Accounts can be Compromised: Messages from known contacts may still be unsafe if their accounts are hijacked.
4) Avoid Unexpected Downloads: Only download files you were clearly expecting from trusted senders.
5) Dismiss Overseas Money Offers: Messages about foreign lotteries, inheritances, or transfers are almost always scams.
Conclusion
Knowing What is Social Engineering helps you stay one step ahead of attackers who exploit trust, not technology. By recognising red flags, questioning unexpected requests, and building smart security habits, you can protect your data, avoid costly mistakes, and create a stronger, more security-aware digital environment.
Build essential skills to protect systems, data, and networks with the Cyber Security Training – Join now!
Frequently Asked Questions
What is the Biggest Risk to Social Engineering Attacks?

The biggest risk is human error. Social Engineering relies on manipulating people’s emotions such as trust, fear, or urgency. A single click on a malicious link or sharing sensitive information without verifying the source can give attackers full access.
What is the Difference Between Phishing and Social Engineering?

Phishing is a type of Social Engineering that uses fake emails, messages, or websites to trick users into giving away data. Social Engineering is broader and includes any tactic that manipulates human behaviour, online or offline to exploit information.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including the Social Engineering Training, Fraud Analytics Training, and Malware Analysis Training. These courses cater to different skill levels, providing comprehensive insights into ARP Spoofing.
Our IT Security & Data Protection Blogs cover a range of topics related to Social Engineering, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

The Knowledge Academy is a world-leading provider of professional training courses, offering globally recognised qualifications across a wide range of subjects. With expert trainers, up-to-date course material, and flexible learning options, we aim to empower professionals and organisations to achieve their goals through continuous learning.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Social Engineering Training
Social Engineering Training
Fri 26th Jun 2026
Fri 14th Aug 2026
Fri 18th Sep 2026





 Top Rated Course
Top Rated Course








 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


