We may not have the course you’re looking for. If you enquire or give us a call on 0800 446148 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Protecting applications has become one of the biggest priorities for modern organisations. As businesses rely more on software, mobile apps, cloud platforms, and online services, the risks they face also grow. Cyber attackers constantly look for weaknesses in applications, hoping to steal data or damage systems. This is where Application Security plays a vital role.
It focuses on building, testing, and maintaining software in a way that keeps it safe from threats. In this blog, we’ll explore What is Application Security, why it matters, the key processes involved, and the tools that help keep applications safe. Let’s begin to safeguard your applications!
Table of Contents
1) What is Application Security (AppSec)?
2) Why Application Security (AppSec) is Important?
3) Types of Application Security (AppSec)
4) What are the Application Security Processes?
5) When Should Application Security Testing be Performed?
6) What are the Application Security Testing Tools?
7) Application Security (AppSec) Best Practices
8) Conclusion
What is Application Security (AppSec)?
Application Security, also known as AppSec, refers to the processes, tools, and practices used to identify, fix, and prevent vulnerabilities in software applications. It covers every stage of the Software Development Lifecycle (SDLC), from initial stages to deployment and ongoing maintenance. Its goal is to stop attackers from gaining unauthorised access, manipulating data, or exploiting weaknesses in the application.
AppSec has become an essential part of software engineering as applications grow more complex and interconnected. At its core, it aims to protect both sensitive data and application code from theft, misuse, or manipulation.
Why Application Security (AppSec) is Important?
Application Security is important because applications have become the main way users interact with businesses, making them a prime target for cyberattacks. A single vulnerability can expose sensitive data, cause financial loss, damage reputation, or lead to legal issues.
To prevent and avoid such things, reduce the possible risks and build trust among the users, you need to have strong Application Security practices and measures. This means your apps can support long-term business growth.
Types of Application Security (AppSec)
In order to protect apps from different forms of cyber threats, the Application Security process comes with different types. The following are those types:
1) API Security
Application Programming Interface (API) security protects communication channels that allow different applications or systems to talk to each other. APIs often carry sensitive information, so they need strict controls to ensure only trusted users or systems can access them.
This type of security may involve encryption, authentication, access checks, and continuous monitoring. It also protects APIs from common threats such as injection attacks, unauthorised access, or improper data handling.
2) Cloud Native Application Security
Cloud native Application Security focuses on protecting applications built for cloud environments. These apps often use containers, microservices, and automated deployment pipelines. Because they are dynamic and distributed, they require different types of protection.
Security measures include scanning container images, checking cloud configurations, monitoring workloads, and managing identities throughout the application’s lifecycle. This helps ensure that cloud-based applications remain secure from development to deployment.
3) Web Application Security
Web Application Security protects applications that users access through a browser. These apps are open to the public, which makes them a target for hackers. Web AppSec includes protecting against SQL injection, cross-site scripting, broken authentication, and session attacks.
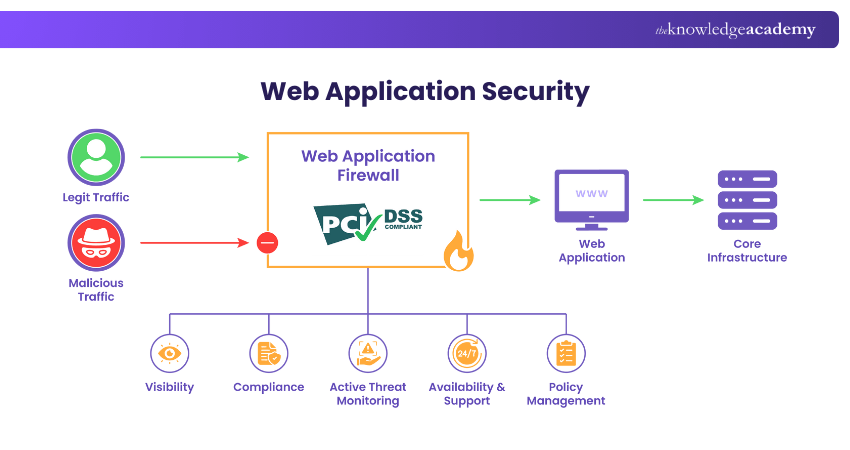
Using input validation, encryption, strong passwords, and regular testing helps keep web applications safe and stable.
4) Mobile Application Security
Mobile Application Security protects apps on smartphones and tablets, which often store personal or financial data. It focuses on securing local data, protecting network communication, using safe libraries, and preventing reverse engineering.
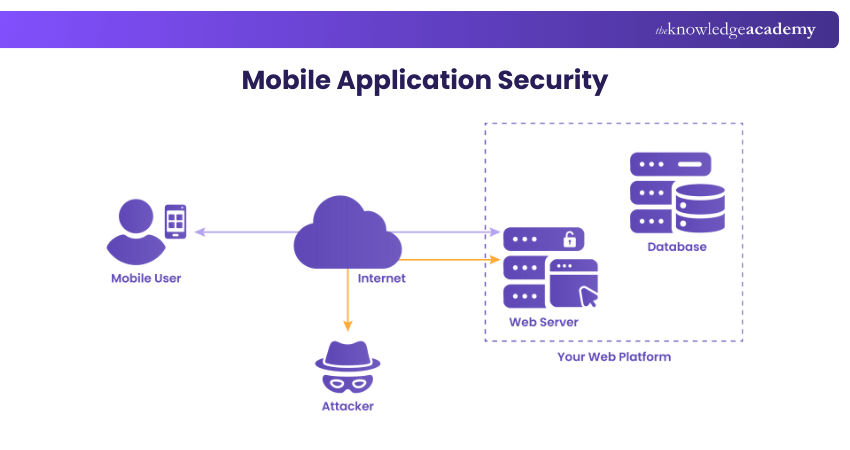
It also addresses risks from unsafe permissions or rooted devices. Using a Virtual Private Network (VPN) strengthens security by encrypting mobile traffic and reducing interception.
Upgrade your .NET Application Security skills with our Certified Application Security Engineer (CASE .NET) Certification– Register today!
What are the Application Security Processes?
Now that you understand what Application Security is and the types involved, here is a clear explanation of how the process works:
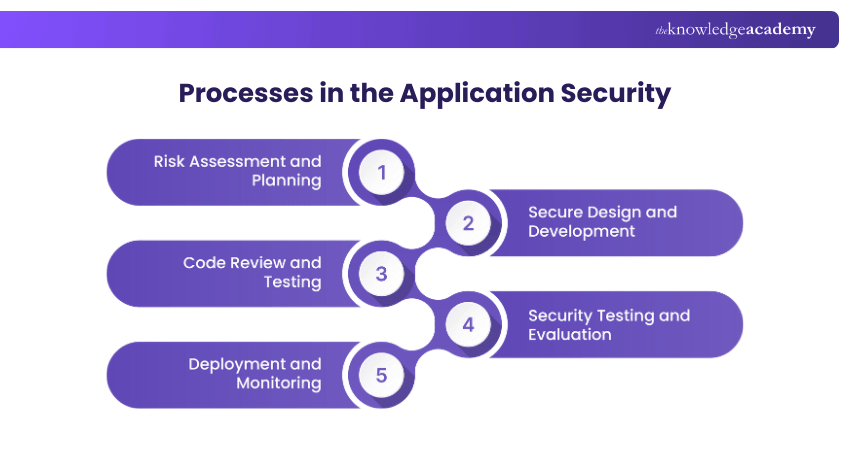
1) Risk Assessment and Planning
The risk assessment and planning process is about finding possible threats or weak spots in the application. It helps the team understand what needs protection and which risks are most important. It also sets the security goals and tools needed during development.
1) Find out what could go wrong or be attacked
2) Decide what security the app needs
3) Rank risks from most serious to least
4) Choose the right tools to protect the app
2) Secure Design and Development
This process ensures that the app is built safely from the beginning. Developers use safe coding rules and think about how to protect data before writing any code. They plan strong login systems, access controls, and safe ways to handle sensitive information.
1) Follow safe coding rules
2) Think about possible threats before building
3) Handle sensitive data carefully
4) Avoid using unsafe or outdated libraries
3) Code Review and Testing
Code review and testing check if the application code is safe and written correctly. Developers review the code to find mistakes or weak areas. Automated tools also scan the code for known risks. Regular testing helps fix the problems early, especially when new features are added.
1) Use tools to scan for security issues
2) Check all third-party libraries for risks
3) Test new features before adding them
4) Write down issues clearly so they can be fixed fast
4) Security Testing and Evaluation
This checks how well the apps stand up to attacks. This includes scanning for weaknesses and testing the app the same way hackers would like penetration testing, vulnerability scanning, and security risk assessments. The goal is to find weak points and fix them before attackers do.
1) Run scans to find weaknesses
2) Check if security controls work properly
3) Fix high-risk issues first
4) Test again after fixes to make sure problems are fixed
5) Deployment and Monitoring
This stage protects the app once it goes live. It includes setting up secure servers, applying correct settings, and using safe third-party tools. After launch, monitoring helps find suspicious activity early, so teams can respond quickly. It also keeps the app stable and compliant.
1) Watch logs for strange or risky behaviour
2) Apply updates and patches regularly
3) Use alerts to act quickly when problems appear
4) Check security and performance often to keep the app safe
Protect sensitive information more effectively with our Certified Encryption Specialist Certification – Join now!
When Should Application Security Testing be Performed?
The testing of the Application Security has to be conducted at every development phase rather than just the end phase. If the teams postpone till the last phase, the problems will be more difficult and costly to solve.
It is necessary to start testing from the planning and designing phase so that the problems are detected early. It is to be a regular process throughout the production, quality assurance, and at that moment the app is about to go live. Even upon the app launching, testing should proceed. Security checks, monitoring, and reviews on regular timing can make the app secure over time.
What are the Application Security Testing Tools?
Application Security testing uses a range of tools to detect weaknesses in an application and fix them before attackers exploit them. These tools help teams assess safety, identify risks early, and strengthen overall protection. Below are some of the main AppSec testing tools:
1) Interactive Application Security Testing (IAST)
IAST checks applications while they are running and gives real-time information about security issues. It works inside DevOps pipelines and automatically tests vulnerabilities to confirm whether they are real and exploitable. IAST is useful for complex applications because it provides accurate and detailed insights into potential weaknesses.
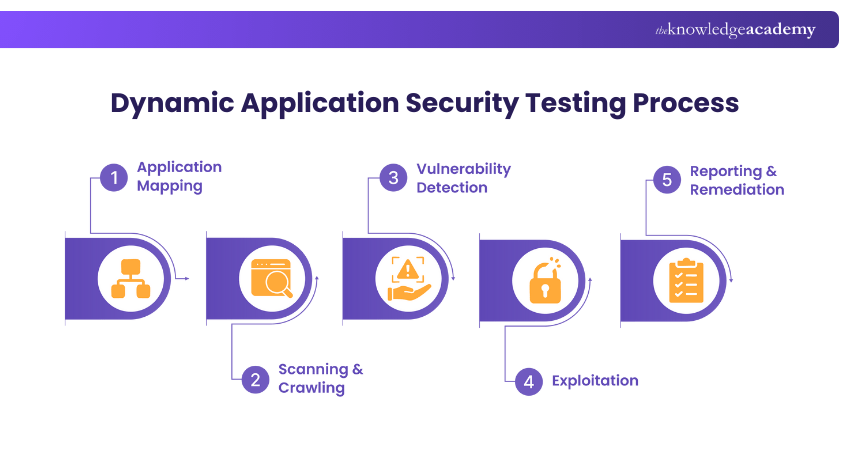
2) Dynamic Application Security Testing (DAST)
DAST tools test applications from the outside by simulating real attacks. They send malicious input to the app to see how it responds. It helps find vulnerabilities like injection errors, authentication problems, and misconfigurations. It is useful for low or medium risk applications and helps meet regulatory requirements.
3) Static Application Security Testing (SAST)
SAST tools analyse the source code before the application runs. They detect insecure functions, unsafe coding patterns, and logic errors. SAST helps developers fix issues early in the development cycle, making it easier to avoid common vulnerabilities that otherwise appear after deployment.
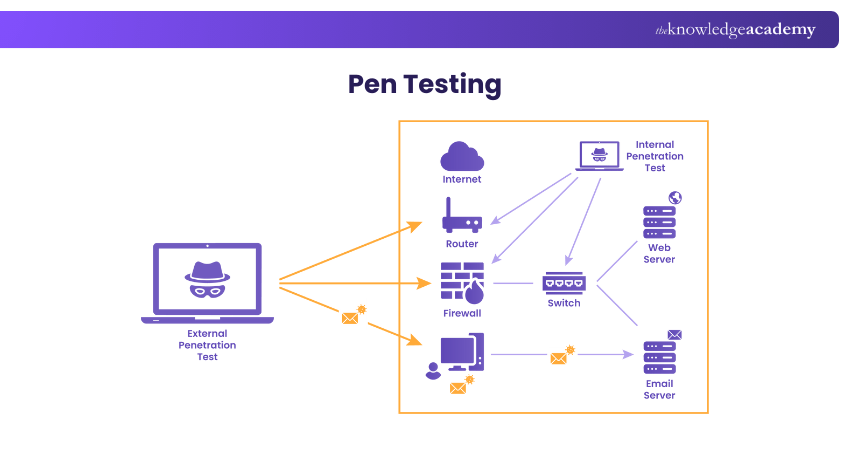
4) Pen Testing
Penetration testing is a manual method where security experts try to break into an application just like real attackers would. It is best for high-risk or business-critical apps, especially those going through major updates. Pen tests uncover advanced attack paths and logic flaws that automated tools may miss.
5) Software Composition Analysis (SCA)
SCA checks all open source and third-party components used in an application. It identifies security risks, outdated libraries, and license compliance issues. Since many applications rely heavily on external code, SCA helps teams keep their software safe. SCA tools also help teams quickly identify risks and recommend updates or safer versions.
Gain the skills to detect and respond to network threats with our Certified Network Defender Certification – Sign up soon!
6) Web Application Firewalls (WAFs)
Web application firewalls protect apps by filtering and monitoring HTTP traffic between the app and the internet. They detect and block common attacks such as SQL injection, cross-site scripting, and cross-site request forgery. By stopping harmful requests before they reach the app, WAFs help prevent data breaches and unauthorised access.
7) Runtime Application Self-protection (RASP)
RASP tools protect applications while they are running and find any suspicious or harmful activity. They work from inside the application and that helps them to respond to attacks in real time. Some RASP solutions can also block malicious actions as soon as they appear, giving the app an extra layer of protection even if other defences fail.
8) Mobile Application Security Testing (MAST)
MAST tools focus on finding vulnerabilities in mobile apps. They analyse how apps store data, handle communication, and use third-party libraries. MAST also checks for unsafe configurations or weaknesses introduced by the device’s Operating System. This helps ensure mobile apps remain safe across different devices and versions.
Application Security (AppSec) Best Practices
Application Security best practices focus on building strong, safe habits throughout development. The following are some practices that you can implement:
1) Start security early in the development process to fix problems before they grow
2) Follow secure coding habits and safe development practices
3) Use automated scans and tools to spot vulnerabilities quickly
4) Review code regularly to catch mistakes or security gaps
5) Remove unnecessary features that increase risk
6) Maintain clear documentation for security processes.
7) Run regular audits, penetration tests, and security reviews
8) Respond quickly to suspicious alerts or activity
9) Check logs often for unusual patterns or threats
10) Retest fixes and patches to confirm vulnerabilities are resolved
Conclusion
Application Security plays an inevitable role in modern software development. As digital services grow and threats evolve even more, organisations have to take steps to protect their applications from harm. When you know exactly What is Application Security, you will never miss investing for it to be better prepared for the future.
Enhance your Cyber Security knowledge with our EC – Council Certification – Start today!
Frequently Asked Questions
What are the Three Pillars of Application Security?

The three pillars of Application Security are:
1) Confidentiality
2) Integrity
3) Availability
How Does API Security Work?

API security works by using authentication, authorisation, encryption, and access controls to protect APIs. It ensures that only trusted users can access the system. This also includes scanning for vulnerabilities, blocking suspicious requests, and monitoring traffic to prevent attacks.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various EC – Council Certification, including Certified Application Security Engineer (CASE Java) Certification, Certified Encryption Specialist Certification and Certified Network Defender Certification. These courses cater to different skill levels, providing comprehensive insights into Vulnerability Management.
Our IT Security & Data Protection Blogs cover a range of topics related to Application Security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Application Security Engineer (CASE Java) Certification
Certified Application Security Engineer (CASE Java) Certification
Mon 21st Sep 2026
Mon 14th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


