We may not have the course you’re looking for. If you enquire or give us a call on +34 932716793 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Data breaches, strict regulations, and rising cyber threats have made security a business priority. Organisations today must do more than install firewalls; they must prove they meet recognised standards. That’s where Cyber Security Compliance becomes essential.
It’s not just about ticking boxes, but about building a culture of accountability and resilience. From protecting customer data to avoiding costly penalties, compliance shapes how businesses operate securely. Let’s explore what it really means and why it matters more than ever.
Table of Contents
1) What is Cyber Security Compliance?
2) Implementing Cyber Security Compliance
3) Key Security Compliance Frameworks and Regulations
4) Key Elements of Cybersecurity Compliance
5) Importance of Compliance in Cyber Security
6) The Challenge of Cybersecurity Compliance
7) What are the Reputational and Operational Risks When Compliance Fails?
8) Conclusion
What is Cyber Security Compliance?
Cyber Security Compliance is the adherence of an organisation with the set laws, regulations and industry standards that are set to safeguard the digital systems and sensitive information. It offers a systematic way of detecting, controlling, and mitigating cyber risks. Through alignment, businesses are able to have accountable and consistent security practices.
It is also through compliance that organisations will know their role in the law and will prevent administrative fines. It shows the customers, partners, and stakeholders that the issue of data protection is taken seriously. Finally, it enhances trust and ensures business resilience and continuity in the long term.
Implementing Cyber Security Compliance
Cybersecurity compliance focuses on implementing specific framework standards within an enterprise that stores and manages sensitive data. These standards are determined based on an analysis of the business's working environment, policies, and the type of data processed within the organisation. Once the enterprise's needs are identified, certain steps are followed to ensure compliance with cyber-security standards and Cyber Security Laws.
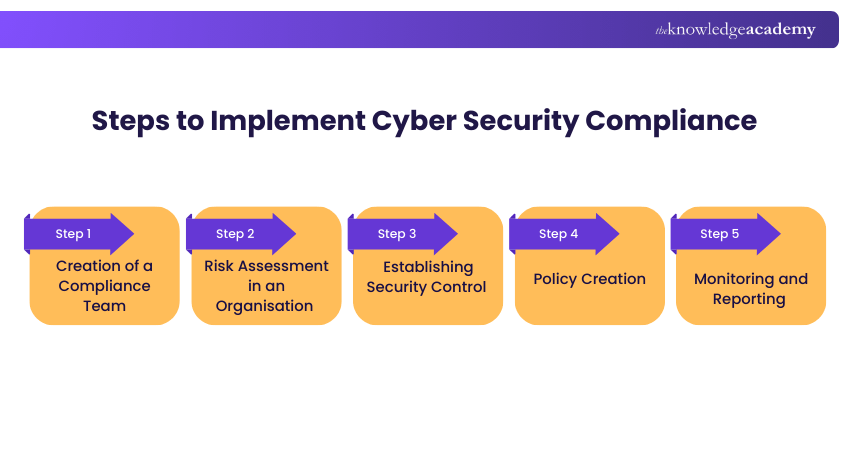
1) Creation of a Compliance Team
Creating a dedicated team is the first step in implementing a cyber‑security standard. This team ensures compliance and strengthens the organisation’s security posture. As businesses increasingly operate virtually, the team must integrate closely with all departments to maintain consistent protection against cyber threats.
2) Risk Assessment in an Organisation
The next step is to evaluate the organisation’s existing cyber‑security architecture. This allows the compliance team to identify current weaknesses and areas for improvement. The assessment typically covers the enterprise’s data, systems and networks. Identified flaws are then prioritised based on legal and protection requirements, and the compliance team strengthens security measures accordingly.
Learn to detect and remove malware using real-world analysis. Join our Malware Analysis Training today!
3) Establishing Security Control
Once the risk and risk levels have been evaluated, necessary changes are made within a company. These changes come in the form of security-based controls that check for authorisation on different levels. Some examples of such security-based controls are password-based access, Data Encryption Standard for secure encryption, metric identification such as optical and fingerprint detection, and firewalls within the network.
4) Policy Creation
Security compliances act as benchmarks, but they only work when effectively implemented. Even the best framework is useless without proper physical and social application. Physical implementation occurs through security controls, while social implementation is achieved through organisational policies. These policies guide employees during incidents like data breaches and are regularly updated to address emerging threats.
5) Monitoring and Reporting
A strong cybersecurity framework today may still be vulnerable tomorrow because threats evolve as technology advances. New vulnerabilities can lead to zero-day attacks, and attackers may strengthen old methods, such as combining previous ransomware variants. Continuous monitoring of networks and systems is essential to detect issues early. When incidents like data breaches are identified quickly, the compliance team can respond and develop new countermeasures.
Key Security Compliance Frameworks and Regulations
Organisations operate within a diverse landscape of cybersecurity laws and frameworks. Each addresses specific industries, risk areas, or data protection requirements. Understanding these regulations is essential to maintain compliance and avoid financial, legal, and reputational consequences.
Industry-specific Regulations
Certain sectors must comply with regulations tailored to the sensitive data they handle. These mandates strengthen security controls and help maintain stakeholder trust.
a) Health Insurance Portability and Accountability Act (HIPAA): A U.S. law that protects patient health information by requiring administrative, physical, and technical safeguards to ensure data security.
b) Payment Card Industry Data Security Standard (PCI DSS): A global standard for organisations that process or store cardholder data, enforcing strict controls to reduce payment fraud.
c) Cybersecurity Maturity Model Certification (CMMC): A U.S. Department of Defense framework that assesses the cybersecurity maturity of defence contractors handling federal information.
Wish to learn more about Cyber threats? Take our course in Cyber Security Awareness.
Global and Regional Data Protection Laws
Data protection laws govern how personal information is collected, processed, and stored. They prioritise transparency, accountability, and individual privacy rights.
a) General Data Protection Regulation (GDPR): An EU regulation that sets strict requirements for handling the personal data of EU residents and applies to organisations worldwide.
b) California Consumer Privacy Act (CCPA): A U.S. state law granting California residents rights to access, delete, and control the sale of their personal data.
Foundational Cybersecurity Frameworks
Beyond regulations, widely adopted frameworks guide organisations in managing cyber risk. They provide structured best practices adaptable to different environments.
a) NIST Cybersecurity Framework (CSF): A voluntary framework that helps organisations manage risk through five core functions: Identify, Protect, Detect, Respond, and Recover.
b) ISO/IEC 27001: An international standard for Information Security Management Systems, offering a systematic approach to managing and mitigating information security risks.
c) Center for Internet Security (CIS Controls): A globally recognised set of prioritised security actions designed to strengthen organisational cyber defences.
Key Elements of Cybersecurity Compliance
Complying with cybersecurity regulations helps organisations validate their security controls and strengthen their overall defence posture. It reduces the risk of data breaches, protects sensitive information, and minimises legal or financial penalties. Key elements of compliance include:
a) Regulatory Requirements: Meeting legal obligations specific to an industry or region, such as General Data Protection Regulation, Health Insurance Portability and Accountability Act, or California Consumer Privacy Act.
b) Industry Standards: Aligning with recognised frameworks like ISO/IEC 27001, NIST Cybersecurity Framework, and Payment Card Industry Data Security Standard to implement structured security practices.
c) Policies and Procedures: Establishing internal security policies and operational procedures that reflect regulatory and industry requirements.
d) Risk Management: Conducting regular risk assessments to identify vulnerabilities and applying controls to mitigate threats.
e) Access Control: Restricting system and data access to authorised users based on defined roles and responsibilities.
f) Data Protection: Implementing safeguards such as encryption, backup, and secure storage to prevent unauthorised access or breaches.
g) Incident Response: Developing and maintaining a response plan to detect, manage, and recover from security incidents efficiently.
h)Training and Awareness: Educating employees on cybersecurity responsibilities and compliance obligations through ongoing programmes.
i) Auditing and Monitoring: Continuously reviewing systems, processes, and third parties to ensure ongoing compliance and improvement.
j) Reporting and Documentation: Maintaining accurate records to demonstrate compliance readiness and support regulatory audits.
Importance of Compliance in Cyber Security?
Strong compliance with cyber security has many benefits, not limited to simply being well-defended from cyber-attacks. Some of such alternative benefits are as follows.
a) Positive Public Reputation: Compliance with cyber security standards promises a good reputation. This results in gaining customers' trust and thus gaining loyal customers.
b) Legal Obligations: Cyber security compliance is mandated by law in the majority of locations across the globe. The guiding standard for these laws may vary, but it is generally a good idea to abide by legal regulations and compliance. Many of these laws also impose heavy penalties for failing to adhere to them.
c) Reliable and Trustworthy Business: A well-defended business will earn customer trust and be a more reliable choice for other businesses and partnerships.
d) Efficient Architecture: Cyber security compliance rigorously analyses the state of network architecture. Hence, any changes made within it result in more streamlined data and better data flow. This benefits the working process and data handling within the company, hence increasing the overall productivity.
e) Advantage Against the Competition: In this competitive day and age, people can choose a service from many options. Thus, customers are more likely to choose services from a company with databases better defended from cyber-attacks, giving a business a competitive edge.
Gain hands-on experience developing cyber risk strategies and response plans. Join our Cyber Security Risk Management Training now!
The Challenge of Cybersecurity Compliance
Cybersecurity compliance requires organisations to continuously manage risk while aligning security efforts with regulatory expectations. As threats evolve and compliance demands increase, businesses must adopt a structured, risk-based approach supported by visibility, automation, and operational efficiency. Key challenges include:
a) Identify and address data risks and system vulnerabilities while aligning them with business and regulatory objectives.
b) Provide visibility and enforce security controls to demonstrate their effectiveness in meeting compliance requirements.
c) Adopt a prioritised, risk-based approach to cybersecurity compliance efforts.
d) Automate and streamline data security and privacy programmes to reduce manual effort.
e) Eliminate compliance silos and reduce control clutter to enable faster, informed executive decision-making.
f) Minimise security assessment control creep across frameworks and audits.
g) Reduce administrative burden and improve the efficiency of personnel managing security risks.
h) Lower the cost of recurring security and IT audits or assessments.
What are the Reputational and Operational Risks When Compliance Fails?
When cybersecurity compliance fails, the consequences extend far beyond regulatory penalties. Organisations may experience operational disruption, financial setbacks, and long-term reputational damage that can be difficult to recover from. Key risks include:
a) Loss of Customer Trust
b) Brand Reputation Damage
c) Operational Downtime
d) Supply Chain Disruption
e) Regulatory Fines and Legal Action
f) Increased Recovery and Remediation Costs
Conclusion
Strong security is no longer optional in a digitally driven world. Prioritising Cyber Security Compliance helps organisations reduce risk, protect trust, and stay resilient against evolving threats. By embedding compliance into everyday operations, businesses can turn regulatory demands into a strategic advantage.
Interested in becoming a Cyber-Security specialist? Join our Cyber Security Training course!
Frequently Asked Questions
Why is ongoing cybersecurity compliance crucial, and not just a one-time achievement?

Ongoing compliance is essential because the threat landscape constantly evolves, new vulnerabilities emerge, and regulations are frequently updated. Continuous adherence ensures sustained protection, helps organisations adapt to new risks, and avoids legal repercussions.
What are the consequences of non-compliance with cybersecurity regulations?

Non-compliance can lead to significant financial penalties, legal liabilities, and reputational damage, as well as loss of customer trust and operational disruption. Organisations may also become more vulnerable to cyberattacks and data breaches due to weaker security controls.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including the Certified Cyber Security Professional Training, Cyber Security Awareness Course, and Digital Forensics Training. These courses cater to different skill levels, providing comprehensive insights into Symmetric Encryption.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Security Compliance, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Risk Assessment skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 24th Jul 2026
Fri 9th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


