We may not have the course you’re looking for. If you enquire or give us a call on +49 8000101090 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Information is one of the most valuable assets owned by any organisation. From customer data to intellectual property, every piece of information must be protected from threats, breaches, and misuse. This is where ISO 27001 Annex A Controls provide a clear direction, giving a structured set of safeguards designed to manage risks and strengthen Information Security.
Understanding these security controls is essential for turning risk assessment findings into practical actions that strengthen your organisation’s security framework. In this blog, you will learn about ISO 27001 Annex A Controls, their themes, and more. Read on to gain a clear and practical understanding.
Table of Contents
1) What are ISO 27001 Annex A Controls?
2) ISO 27001: 2013 vs ISO 27001: 2022 Annex A Changes
3) What are the 4 Themes of ISO 27001?
4) A 5.1–5.37: Organisational Controls
5) A 8.1–8.34: Technological Controls
6) How to Implement ISO 27001 Controls?
7) What is a Statement of Applicability?
8) Why Does Annex A Start with Control Number 5 in ISO 27001?
9) Are Annex A Controls Mandatory?
10) Conclusion
What are ISO 27001 Annex A Controls?
ISO 27001 Annex A Controls are a structured set of 93 Information Security controls defined in ISO/IEC 27001:2022 to help organisations manage and reduce security risks. These controls include policies, procedures, and technical measures designed to protect sensitive information from threats like unauthorised access and data breaches.
They are grouped into four categories: organisational, people, physical, and technological controls. Organisations select relevant controls based on their risk assessment and business needs. The chosen controls are documented in the Statement of Applicability (SoA), which justifies their inclusion or exclusion.
ISO 27001: 2013 vs ISO 27001: 2022 Annex A Changes
ISO 27001: 2022 introduced important updates to Annex A to address emerging security challenges and evolving technologies. The revised version streamlines the control structure and introduces new controls that reflect modern security risks. Let's look at how the controls are grouped in the latest version and the newly introduced controls below:
1) How the Controls are Grouped?
In ISO 27001: 2022 Annex A Controls are structured into a streamlined set of 93 controls, which is reduced from 114 controls across 14 domains in the 2013 version. These controls are grouped into four categories:
1) Organisational Controls: 37 controls
2) People Controls: 8 controls
3) Physical Controls: 14 controls
4) Technological Controls: 34 controls
The revised grouping improves clarity and reflects modern security priorities. Organisational controls focus on governance, policies, and risk management. People controls address responsibilities, awareness, and human-related risks. Physical controls protect buildings, equipment, and secure areas from unauthorised access. And, finally, Technological controls safeguard systems, networks, and data through digital security measures.
2) The 11 Newly Introduced Controls
ISO 27001: 2022 introduced 11 new controls to address evolving cyber threats, cloud adoption, and advanced technologies. It includes:
1) A.5.7 Threat Intelligence: Enables organisations to proactively identify, analyse, and respond to emerging security threats.
2) A.5.23 Information Security for Use of Cloud Services: Ensures secure governance and management of cloud environments.
3) A.5.30 ICT Readiness for Business Continuity: Prepares organisations to maintain critical IT services during disruptions.
4) A.7.4 Physical Security Monitoring: Strengthens protection of physical locations through monitoring systems.
5) A.8.9 Configuration Management: Ensures secure and consistent system configurations.
6) A.8.10 Information Deletion: Establishes secure processes for permanently deleting sensitive information.
7) A.8.11 Data Masking: Protects sensitive data by obscuring it during processing or storage.
8) A.8.12 Data Leakage Prevention: Minimises the risk of unauthorised data exposure.
9) A.8.16 Monitoring Activities: Enhances visibility and detection of security incidents.
10) A.8.23 Web Filtering: Protects against web-based threats by controlling access to unsafe sites.
11) A.8.28 Secure Coding: Promotes secure software development practices to prevent vulnerabilities.
These additions strengthen organisational resilience by addressing modern risks, such as cloud dependency, data leakage, and cyber threats. They are valuable for industries such as finance, healthcare, and IT, where cloud services and advanced technologies play a critical role.
What are the 4 Themes of ISO 27001?
ISO 27001 organises its Annex A controls into four key themes, each focusing on a specific area for effectively managing and securing information across the organisation.
1) Organisational Controls: These address internal policies, governance, and processes to guide the overall management of Information Security risks.
2) People Controls: These focus on staff roles, awareness, and training to ensure individuals understand and fulfil their security responsibilities.
3) Physical Controls: These involve protecting physical spaces and equipment against unauthorised access, theft, or environmental damage.
4) Technological Controls: These cover technical defences like encryption, secure coding, and network protection to safeguard digital systems and data.
Lead audits and drive excellence with ISO 27001 Lead Auditor Training now!
A 5.1–5.37: Organisational Controls
Controls in this section of ISO 27001 outline how an organisation should set up and manage its Information Security responsibilities. They provide direction for creating policies, assigning roles, managing risks, and ensuring secure communication and operations.
Altogether, these controls help build a solid, structured approach to maintaining Information Security across all departments.
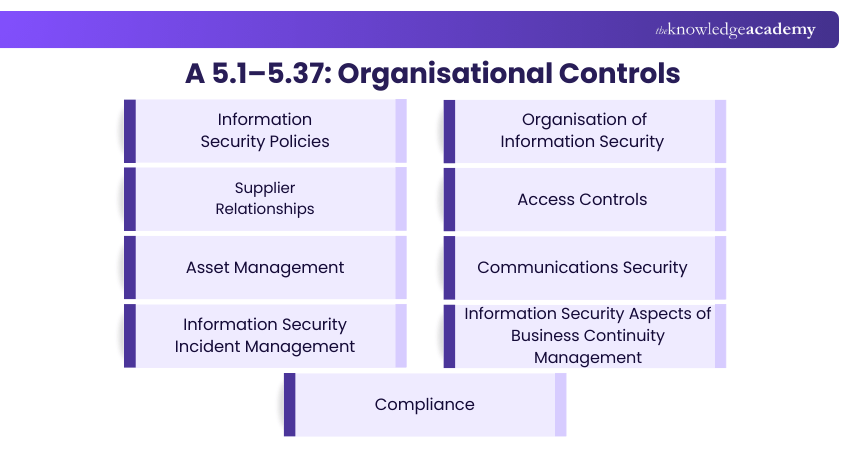
1) Information Security Policies
Organisations must create and maintain clear policies that define their approach to Information Security. These policies should be well-documented, approved by senior management, and shared with staff to ensure consistent practices. They serve as the foundation for all security decisions and actions.
2) Organisation of Information Security
This control focuses on putting the right people and structure in place to manage Information Security. It involves defining roles, assigning responsibilities, and coordinating efforts across the business. It also includes ensuring external partners meet your organisation's security standards.
3) Supplier Relationships
This control ensures that suppliers and partners follow your security expectations. Organisations should set clear terms, monitor third-party performance, and regularly check that suppliers meet agreed security requirements. It helps avoid risks that might come from outside your organisation.
4) Access Controls
To protect sensitive data, organisations must restrict access only to authorised individuals. This involves setting up proper login procedures, managing user permissions, and conducting routine checks. These practices keep information safe and reduce the risk of data breaches.
5) Asset Management
Asset management ensures that all information assets are identified, tracked, and protected. Organisations need to maintain a list of assets, assign ownership, and define how each item should be handled throughout its lifecycle. This control ensures assets are used and disposed of responsibly.
6) Communications Security
This control is about safeguarding data as it moves within the organisation and to external parties. It includes securing networks, using encryption, and setting up protocols for safe communication. These steps help prevent leaks and keep information confidential.
7) Information Security Incident Management
Every organisation needs a clear plan for managing security incidents. This involves identifying possible threats, setting up a reporting system, and defining how to respond and recover. Learning from past incidents is also key to improving future readiness.
8) Information Security Aspects of Business Continuity Management
This control ensures that Information Security is not forgotten during disruptions. It includes planning for emergencies, protecting critical processes, and ensuring that security measures stay active even in a crisis. The goal is to bounce back quickly without compromising data safety.
9) Compliance
Organisations must stay in line with legal, contractual, and regulatory obligations around data protection. This involves knowing the relevant laws, performing regular audits, and responding properly to any breaches. Staying compliant helps avoid fines and keeps trust intact.
Start strong with ISO 27001—join our ISO 27001 Foundation Course and sharpen your security edge!
A 6.1–6.8: People Controls
People control within ISO 27001 address how an organisation manages its workforce from a security standpoint. These measures ensure that employees and contractors are aware of their roles in safeguarding information. From recruitment through to termination, the focus is on minimising risk through responsible human resource practices.
Human Resources Security
This control spans the entire employee lifecycle before joining, during employment, and after departure. It involves background checks, clearly defined job responsibilities, regular security training, and ongoing performance monitoring. Upon exit, access rights must be revoked immediately to prevent any misuse of information.
A 7.1-7.13: Physical Controls
Physical controls are designed to protect an organisation’s buildings, hardware, and other physical assets from harm or unauthorised access. These measures support the protection of both digital and paper-based information, ensuring continuity and security under normal and emergency conditions.
Physical and Environmental Security
This control ensures that physical infrastructure is safeguarded against threats such as theft, intrusion, or natural disasters. Common measures include limiting access to critical areas, using Closed-circuit Television (CCTV) surveillance, and placing equipment in secure locations. It also covers the secure disposal of outdated or damaged hardware.
A 8.1–8.34: Technological Controls
Technological controls are essential for safeguarding an organisation’s digital environment. They provide a structured approach to securing systems, networks, and data using the right technologies. These controls span the entire information lifecycle from system design and development to ongoing maintenance and protection.
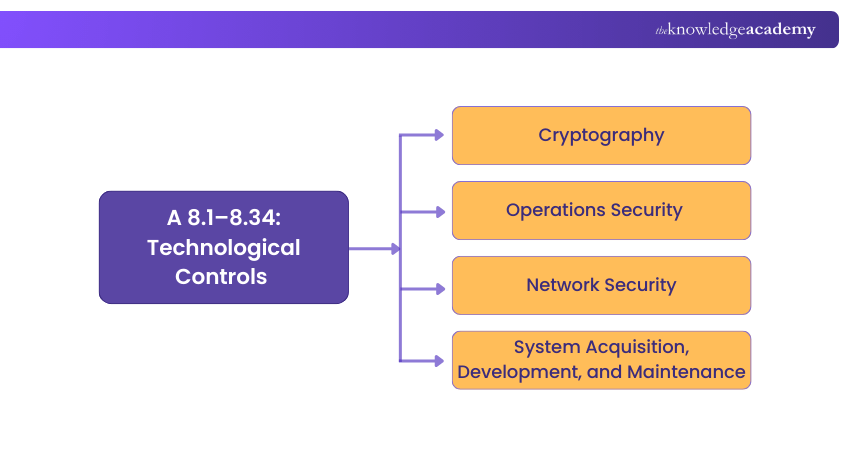
1) Cryptography
This control focuses on applying encryption to keep sensitive information secure. It involves managing cryptographic keys, securing data transmission, and using approved methods to protect data integrity and confidentiality. Even if data is intercepted, proper cryptography prevents unauthorised access.
2) Operations Security
Operations security ensures that day-to-day digital processes run securely. It includes managing system changes, maintaining secure configurations, monitoring activities, and addressing vulnerabilities promptly. These practices help prevent disruptions and unauthorised access while supporting smooth business operations.
3) Network Security
Network security aims to protect information as it flows across internal and external networks. This involves implementing firewalls, using intrusion detection tools, segmenting networks, and configuring systems securely. These measures help guard against breaches and restrict unauthorised access to sensitive data.
4) System Acquisition, Development, and Maintenance
Security should be embedded from the earliest stages of system or software development. This control ensures that all systems are designed, built, and maintained with appropriate security measures in place. It encourages secure coding practices, thorough testing, and regular updates to reduce potential risks.
Audit like a pro—unlock the secrets with our ISO 27001 Internal Auditor Training now!
How to Implement ISO 27001 Controls?
For successfully implementing ISO 27001 Controls, organisations need a structured International Organization for Standardization implementation requirements to ensure risks are identified, addressed, and managed. Let's look at them below:
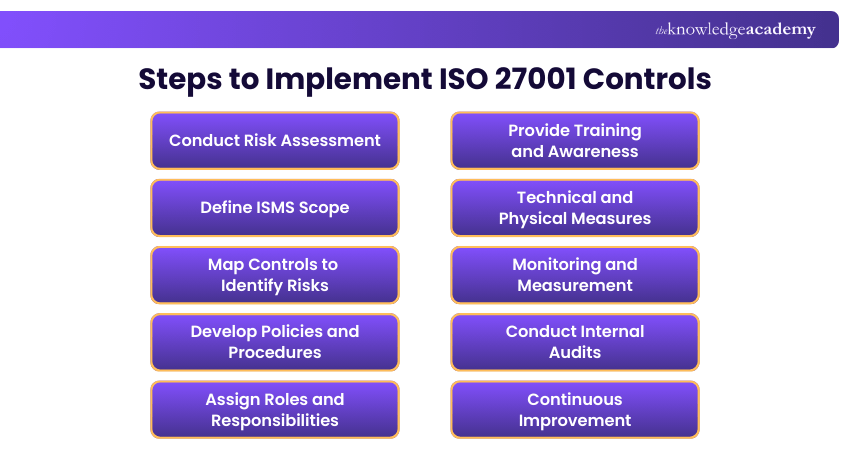
1) Conduct Risk Assessment: Identify and prioritise Information Security risks by evaluating their likelihood and impact, ensuring resources are focused on the most critical threats.
2) Define ISMS Scope: Clarify which assets, processes, and departments are covered by the Information Security Management System (ISMS) to avoid gaps and ensure accountability.
3) Map Controls to Identify Risks: Select relevant controls from Annex A of ISO 27001 and align them directly with identified risks to provide targeted mitigation.
4) Develop Policies and Procedures: Develop documented policies and enforceable procedures that guide daily operations, incident response, and compliance with security requirements.
5) Assign Roles and Responsibilities: Assign clear ownership for each control, ensuring accountability and effective coordination across teams and management.
6) Provide Training and Awareness: Educate employees and contractors on security policies, acceptable practices, and incident reporting to build a culture of security awareness.
7) Technical and Physical Measures: Implement safeguards such as access management, encryption, monitoring systems, and secure facilities to enforce controls in practice.
8) Monitoring and Measurement: Track performance indicators, monitor activities, and measure control effectiveness to ensure compliance and resilience.
9) Conduct Internal Audits: Conduct regular audits to identify weaknesses, nonconformities, and areas for improvement, documenting corrective actions.
10) Continuous Improvement: Update and refine the ISMS based on audit findings, emerging risks, and evolving threats, treating improvement as an ongoing cycle.
What is a Statement of Applicability?
Before proceeding further, it's important to introduce a Statement of Applicability (SoA), which outlines how an organisation plans to implement specific Annex A Controls. In ISO 27001 2022, a Statement of Applicability (SoA) is a critical document listing the Annex A Controls that an organisation will adopt to meet the standard's requirements. This document is essential for organisations aiming for ISO 27001 certification.
Your SoA should include these key elements:
1) A comprehensive list of controls necessary to address Information Security risks, including those from Annex A.
2) Justification for including all selected controls.
3) Confirmation of implementation status.
4) Explanation for any decisions to exclude specific Annex A Controls.
Why Does Annex A Start with Control Number 5 in ISO 27001?
Annex A of ISO 27001 begins at control number 5 to align with ISO/IEC 27002, which provides detailed guidance on implementing each control. This consistency facilitates easy cross-referencing between the two standards and reflects the updated structure introduced in the 2026 revision.
Starting from control number 5 avoids confusion by maintaining the same numbering across related standards, simplifying integration for auditors and implementers. The earlier numbers (1- 4) are reserved for introductory and structural clauses of the standard, supporting a clear and logical flow in documentation and audits.
Are Annex A Controls Mandatory?
Annex A controls are not mandatory in the sense that every control must be implemented. However, all 93 controls must be reviewed during the risk assessment process to determine their relevance to the organisation's risks. If a control is excluded, a valid justification must be documented.
This approach allows flexibility while maintaining a high standard of Information Security. Organisations tailor the controls based on their specific needs, operations, and regulatory requirements, ensuring effective risk management without enforcing unnecessary measures.
Conclusion
ISO 27001 Annex A Controls is about building a resilient, risk-aware organisational culture that protects information assets while enabling business growth. The real value lies in cultivating a culture of continuous improvement where Information Security becomes a driver of trust, compliance, and long‑term business success.
Fortify your business from the inside out— join our ISO 27001 Lead Implementer Training.
Frequently Asked Questions
How do I Select Annex A Controls?

Choosing Annex A Controls involves assessing your organisation's Information Security risks and aligning them with the controls listed in ISO 27001. Consider factors like risk assessment outcomes, legal requirements, and business objectives for effective selection.
Which Annex A Controls Should be Included in my Security Policy?

Include Annex A Controls that address identified risks and support your Information Security objectives. Focus on controls relevant to your organisation's operations, ensuring comprehensive coverage of areas like access control, cryptography, incident management, and physical security.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27001 Training, including the ISO 27001 Foundation Training, ISO 27001 Lead Auditor Training, and ISO 27001 Internal Auditor Training. These courses cater to different skill levels, providing comprehensive insights into Information Security Management.
Our IT Security & Data Protection Blogs cover a range of topics related to ISO 27001, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Information Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Hailey Davis is an ISO compliance expert with over 10 years of experience in audit, quality management systems (QMS), and regulatory compliance. She has worked with various industries, including manufacturing, healthcare, and technology, ensuring organisations achieve and maintain ISO certifications. Hailey’s content provides practical, actionable insights on navigating compliance challenges and improving business processes.
View Detail
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 ISO 27001 Foundation
ISO 27001 Foundation
Mon 6th Jul 2026
Mon 3rd Aug 2026
Mon 7th Sep 2026
Mon 5th Oct 2026
Mon 2nd Nov 2026
Mon 7th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


