We may not have the course you’re looking for. If you enquire or give us a call on +44 1344 203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Information moves faster than ever, but with speed comes risk. From personal data leaks to major company legal breaches, security failures can be costly and damaging. That is why it leads to the one important question: What is Information Security, and why does it matter to everyday work and life?
It is about safeguarding your data wherever it lives or travels, protecting sensitive information using clear policies, strong controls, and practical security principles. These measures keep data secure and private. In this blog, you will explore What is Information Security, its types, principles, and more.
Table of Contents
1) What is Information Security?
2) Principles of Information Security
3) Types of Informational Security
4) Difference Between Cybersecurity and Information Security
5) Policies of Information Security
6) Measures of Information Security
7) What is Information Security in a Nutshell?
8) Conclusion
What is Information Security?
Information Security is the practice of protecting important information from unauthorised access, disclosure, misuse, alteration, or disruption. It ensures that sensitive data is only seen and used by the authorised people, remains accurate, and is available when needed. Its primary focus is to keep organisational and personal data confidential, intact, and accessible.
Information assets can include financial records, personal details, confidential business data, paper documents, digital files, and more, covering the entire data lifecycle. As threats keep rising and hybrid and multi-cloud systems grow, InfoSec continues to evolve, requiring teams, tools, and processes to work together.
Principles of Information Security
The principles of Information Security provide a structured foundation for protecting data and systems against misuse, loss, and tampering. Let’s look at the three major principles used in practice below:
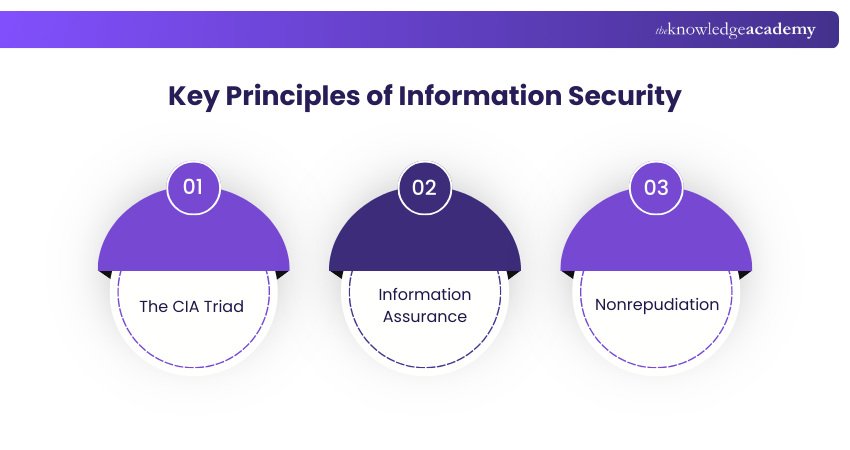
1) The CIA Triad
The CIA Triad stands for confidentiality, integrity, and availability. These three pillars of the CIA triad form the foundation of most security systems and controls. It helps organisations identify vulnerabilities and build targeted safeguards. Usually, when people ask about What is Information Security, these three pillars sit at the centre of the answer. Let's explore them below:
1) Confidentiality
Confidentiality ensures that information is accessed only by authorised users. It protects sensitive data from unauthorised viewing or disclosure through controls such as encryption, strong passwords, access permissions, and authentication mechanisms.
2) Integrity
Integrity ensures that information remains accurate, complete, and unaltered unless modified through authorised actions. It is supported by validation checks, audit logs, hashing techniques, and version control methods that detect or prevent unauthorised changes.
3) Availability
The third pillar ensures information and systems are accessible when needed by authorised users. It is maintained through backups, redundancy, and reliable infrastructure and recovery plans.
2) Information Assurance
Information Assurance (IA) primary focus is to protect and manage risks to information and information systems. It is based on five key pillars: confidentiality, integrity, availability, authenticity, and non-repudiation. It requires layered security controls that protect data during processing and transmission, whether stored in physical systems or cloud environments.
1) Authenticity
Authenticity ensures that information, systems, and users are genuine and not impersonated by unauthorised parties. It verifies the identity of individuals and confirms that data truly comes from a trusted source. Methods such as digital signatures, authentication protocols, and secure certificates help maintain authenticity and protect against identity spoofing.
2) Non-repudiation
Nonrepudiation ensures that a person or system cannot deny performing a digital action or transaction. It provides verifiable proof of origin and activity through mechanisms such as digital signatures, certificates, and audit logs. This is essential for maintaining trust and accountability in digital communications and transactions.
Advance your security architecture skills and design robust enterprise security solutions with CISSP-ISSAP Training now!
Types of Information Security
Information Security encompasses a range of specialised disciplines designed to protect systems and data from various threats. Each type focuses on unique risks and defence strategies to safeguard digital assets effectively.

1) Network Security
This area protects the integrity and usability of your network infrastructure. It includes measures to prevent unauthorised access, misuse, or denial of service attacks, using firewalls, intrusion prevention systems, and encryption.
2) Endpoint Security
Endpoint security secures devices like laptops, desktops, and mobile phones. With the rise of remote work, protecting endpoints against malware, ransomware, and unauthorised access has become crucial.
3) Internet Security
This type focuses on protecting data exchanged online. Measures include secure web gateways, browser protection, and monitoring tools to block phishing sites and malicious downloads. It reduces the risk of users being exposed to harmful websites and online threats.
4) Cloud Security
Cloud security safeguards data and applications hosted in cloud environments. It uses encryption, identity and access management, and security controls tailored to shared responsibility models.
5) Application Security
Application security involves designing software that resists attacks. Practices like secure coding, code reviews, and testing help eliminate vulnerabilities that could be exploited. Security is built into the application lifecycle instead of adding it after deployment.
6) Identity and Access Management (IAM)
IAM ensures only authorised individuals can access systems and data. It incorporates strong authentication, role-based access controls, and privileged account management. Also, it tracks and audits access to reduce misuse and insider threats.
7) Data Security
Data security protects information at rest, in transit, and in use. Encryption, tokenisation, and data masking help prevent data breaches and leaks. It focuses directly on protecting data itself, regardless of where it is stored.
8) Mobile Security
Mobile security safeguards smartphones and tablets against threats such as malware, unauthorised access, and device loss. Mobile device management tools enforce security policies remotely.
9) Disaster Recovery and Business Continuity
These practices ensure systems remain available during disruptions. Strategies include backups, recovery plans, and failover solutions to minimise downtime. They help organisations restore operations quickly after cyber incidents or outages.
10) Operational Security (OpSec)
Operational security focuses on protecting sensitive processes and activities. It includes policies to control how data is handled and shared across the organisation. These types of Information Security work together to create layered protection against evolving cyber threats and help maintain the confidentiality, integrity, and availability of critical systems.
Strengthen your Information Security management expertise and lead security programmes with confidence with ISSMP Training now!
Difference Between Cybersecurity and Information Security
Cybersecurity and Information Security are often used together, but they are not identical. Understanding their differences helps organisations design clearer policies and stronger protection strategies. Let’s look at the differences in the table below:
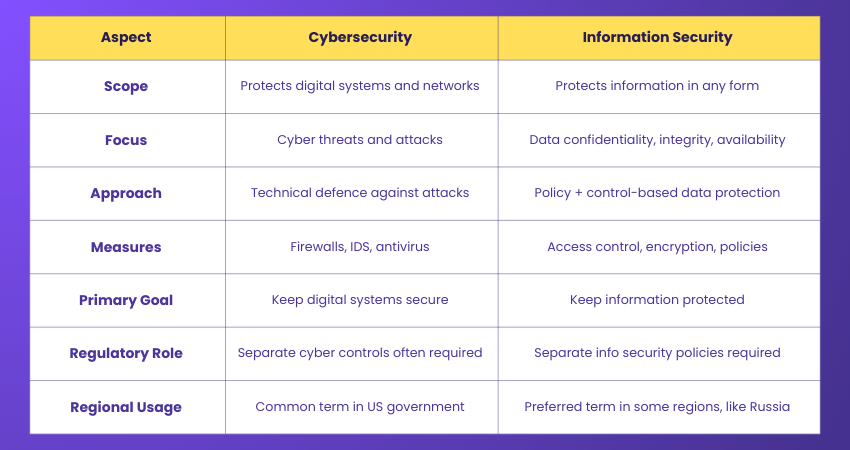
Cybersecurity concentrates on protecting systems from digital attacks that operate in cyberspace, such as networks, servers, or applications. Information Security takes a broader view by protecting information itself in any format, including paper records, verbal communication, and stored media. It uses both technical and administrative controls.
Another key difference lies in governance and terminology. Many regulators expect organisations to maintain separate Cyber Security and Information Security policies, particularly in highly regulated sectors. There are also regional differences in preferred terminology, with some countries and institutions favouring one term over the other. In practice, organisations achieve the strongest protection when both disciplines are applied together.
Policies of Information Security
An Information Security policy is a critical document that outlines an organisation's approach to Information Security. It serves as a foundational framework for defining the rules, responsibilities, and procedures related to safeguarding an organisation's data, information systems, and technology resources.
The policy's primary goal is to make sure the confidentiality, availability and integrity of information assets and to establish a security-conscious culture within the organisation. Here are the key elements typically found in an Information Security policy.
1) Purpose and Scope: Clearly define the purpose of the policy and its scope, indicating the boundaries of the policy's application. It should specify which information and systems are covered.
2) Policy Statement: Present a clear and concise statement of the organisation's commitment to Information Security and the importance of safeguarding information assets.
3) Roles and Responsibilities: Outline the key responsibilities of individuals and teams involved in Information Security, including top management, IT staff, and end-users.
4) Information Classification: Define a classification scheme for categorising information based on its sensitivity and explain how different classifications should be handled and protected.
5) Access Control: Detail access control mechanisms, including user authentication, authorisation, and the principle of least privilege.
6) Data Encryption: Specify when and how data encryption should be used to safeguard sensitive information, both in transit and at rest.
7) Incident Response: Describe procedures for detecting, reporting, and responding to security incidents and breaches.
8) Password Management: Set password policies and guidelines, including password complexity requirements, expiration, and best practices.
9) Physical Security: Address physical security measures such as access control, surveillance, and visitor policies for securing facilities and hardware.
10) Network Security: Define network security measures, including the usage of firewalls, intrusion detection and prevention systems, and secure configurations.
Elevate your cybersecurity career with CISSP Training. Join now to become a certified expert in Information Security!
Measures of Information Security
Organisations must implement a combination of technical, administrative, and physical measures to protect sensitive data and maintain robust Information Security. Effective measures include enforcing strong access controls to ensure only authorised individuals can view or modify critical information. Regular data backups and secure storage practices help organisations recover quickly from data loss or breaches, while endpoint protection and patch management reduce vulnerabilities in devices and systems.
Monitoring tools such as audit logs and real-time threat detection further strengthen defences by identifying unusual activity before it causes damage. Additionally, employee training and clear security policies are vital for promoting awareness and ensuring that everyone understands their role in safeguarding information. Encryption, multi-factor authentication, and incident response plans also play key roles in building a resilient security posture.
What is Information Security in a Nutshell?
Information security (InfoSec) deals with protecting all forms of information, whether digital or physical. Cybersecurity specifically focuses on safeguarding computer systems and digital information, excluding non-digital assets. Network security is a branch of cybersecurity dedicated to securing networks and their components.
Conclusion
Information is one of the most valuable assets any organisation or individual holds, and protecting it is a top priority. From policies and principles to controls and technologies, a strong security foundation prevents loss, misuse, and disruption. Understanding What is Information Security makes it easier to recognise risks, apply the right safeguards, and build a culture where data protection becomes part of everyday practice.
Lead the charge in cybersecurity! Check out our Chief Information Security Officer Training to become a guardian of digital assets and data security!
Frequently Asked Questions
What is Multi-factor Authentication (MFA)?

Multi-factor authentication (MFA) adds extra security by requiring users to provide two or more verification factors, like a password and a code sent to a phone, to confirm their identity before granting access.
What is the Difference Between a Firewall and Antivirus Software?

A firewall controls incoming and outgoing network traffic to block unauthorised access. Antivirus software scans, detects, and removes malicious programs. Firewalls prevent threats from entering, while antivirus tools remove threats already on the device.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various CISSP Training, including CISSP Training, CISSP-ISSAP Training, and ISSMP Training. These courses cater to different skill levels, providing comprehensive insights into What is System Security Plan.
Our IT Security & Data Protection Blogs cover a wide range of topics related to Data Protection, offering valuable resources, best practices, and expert guidance. Whether you are a beginner or looking to advance your Information Security skills, The Knowledge Academy’s diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 CISSP Training
CISSP Training
Mon 8th Jun 2026
Mon 13th Jul 2026
Mon 14th Sep 2026
Mon 2nd Nov 2026
Mon 7th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


