We may not have the course you’re looking for. If you enquire or give us a call on 01344 203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Ever had your smart speaker answer a question you didn’t ask? Or does your Wi-Fi camera blink unexpectedly? In a world where even our toasters, TVs and toothbrushes are online, one weak link can open the door to a cyber nightmare. That’s where the Cyber Resilience Act steps in offering a digital safeguard for every connected device in your life.
In this blog, we’ll explore the importance of cyber resilience, who’s affected by the Cyber Resilience Act, its key components and provisions, implementation strategies, and common challenges. Let's dive into it.
Table of Contents
1) Understanding the Cyber Resilience Act
2) Importance of Cyber Resilience
3) Who will be Affected by CRA
4) Components of the Cyber Resilience Act
5) Provisions of Cyber Resilience Act
6) Implementing Cyber Resilience Strategies
7) Challenges in Implementing Cyber Resilience
8) Entities Affected by the Cyber Resilience Act
9) What are the Three Critical Component of Cyber Resilience?
10) What is the Cyber Resilience Act for Dummies?
11) Conclusion
Understanding the Cyber Resilience Act
The Cyber Resilience Act (CRA) is a proposed regulation by the European Commission to improve Cyber Security and resilience. The CRA mandates that manufacturers and retailers include robust Cyber Security features from the design phase and throughout the product’s lifecycle. This means that products connected to the internet need to meet these standards. The Act addresses the need for better security in digital products and the difficulty consumers and businesses face in determining which products are secure.
Importance of Cyber Resilience Act
Here are some of the key benefits:
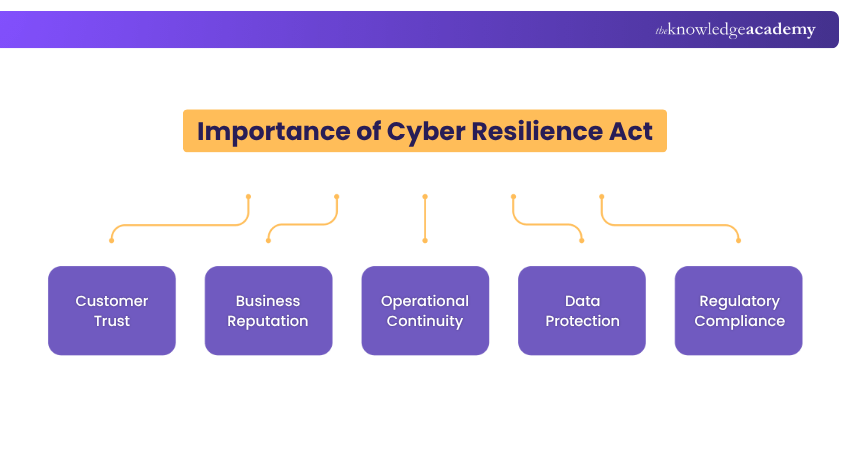
a) Customer Trust: Cyber Resilience is fundamental in maintaining customer trust. When businesses can effectively handle cyber incidents, customers feel more secure in their transactions and interactions.
b) Business Reputation: A company’s reputation is its most valuable asset. Robust Cyber Resilience measures protect a business’s reputation by minimising the impact of Cyber-attacks.
c) Operational Continuity: Cyber Resilience ensures that businesses can continue their operations with minimal disruption. This continuity is vital for maintaining service delivery and economic stability.
d) Data Protection: Protecting sensitive data is a key to Cyber Resilience. It prevents financial loss and protects individuals’ privacy in the event of a data Data Security Breach.
e) Regulatory Compliance: Cyber Resilience helps entities comply with legal and regulatory requirements. Adherence to these standards can prevent costly penalties and legal issues.
Who Will be Affected by CRA
The Cyber Resilience Act will apply to Manufacturers, Importers, and Distributors of Products that have a digital component and require a direct or indirect connection to another device or network, either physically or through data.
A “product with a digital element” refers to any hardware, software, or a combination of both. This includes many everyday items like smartwatches, voice assistants, baby monitors, and other connected devices. Because of this broad definition, the Act covers a wide range of digital products we use in our daily lives.
Components of the Cyber Resilience Act
The Act consists of several key components:
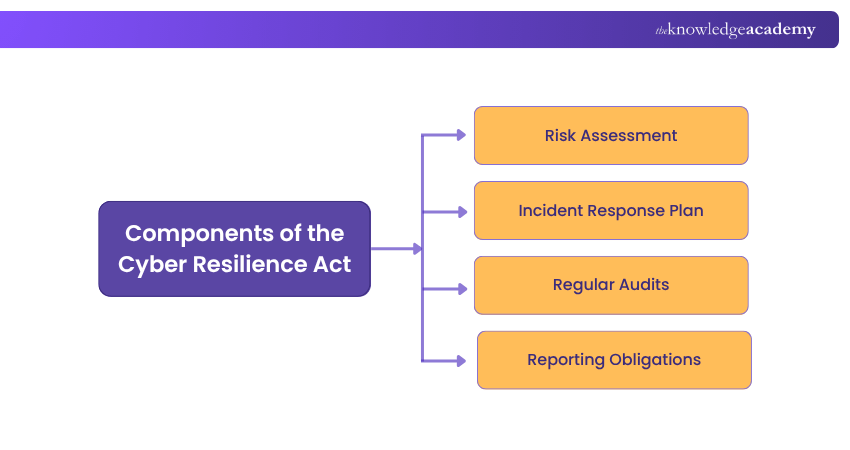
Risk Assessment
Entities are required to conduct thorough Risk Assessments to identify potential cyber threats to their operations. This proactive approach helps in prioritising the risks and implementing appropriate measures to mitigate them. Regular risk assessments also adapt to the evolving nature of cyber threats, ensuring up-to-date defences.
Incident Response Plan
An effective plan is essential for swift action during a cyber incident. It defines the procedures to follow, assigns roles and responsibilities, and outlines communication strategies to minimise damage. A well-rehearsed incident response plan can greatly reduce recovery time, and the costs associated with cyber-attacks.
Regular Audits
Regular audits are essential to verify that cyber resilience measures are properly implemented and effective. These audits assess compliance with the Act and help identify any gaps in the Cyber Security framework. Continuous improvement is supported by insights gained from these audits, thereby strengthening overall Cyber Resilience.
Reporting Obligations
The Act mandates that entities report significant cyber incidents to the authorities in a timely manner. This requirement shows that the authorities are aware of threats and can take necessary actions to prevent further damage. Reporting also contributes to a broader understanding of the cyber threat landscape, which can inform future legislation and protection measures.
Secure your digital landscape with our Cyber Security Risk Management Training- Join today!
Provisions of Cyber Resilience Act
This act includes several key rules designed to strengthen cybersecurity across all covered organisations. These include:
1) Mandatory Reporting:Organisations must report any cybersecurity incidents without delay. This helps detect threats early, respond quickly, and prevent data breaches that could impact national security.
2) Cybersecurity Standards:The Act sets out minimum cybersecurity requirements that businesses must follow. These create a common level of protection, especially for critical infrastructure and sensitive data.
3) Information Sharing:The Act encourages the sharing of cyber threat intelligence between government bodies, private companies, and international partners. Working together in this way improves threat detection and response.
4) Government Collaboration: It promotes stronger cooperation between public agencies and the private sector to manage cyber risks, coordinate responses, and share key security information more effectively.
Implementing Cyber Resilience Strategies
To effectively implement Cyber Resilience strategies, entities should consider the following points:
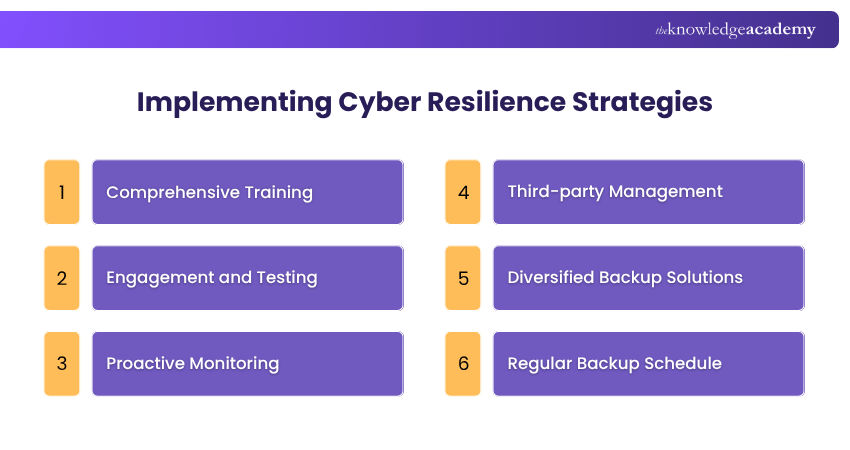
a) Comprehensive Training: Develop a detailed Cyber Security training program that covers a wide range of topics, from password security to recognising phishing attempts.
b) Engagement and Testing: Engage employees with regular Cyber Security drills and tests to evaluate their understanding and readiness to respond to real-world cyber threats.
c) Proactive Monitoring: Implement proactive monitoring systems to automatically detect outdated software and initiate updates.
d) Third-party Management: Ensure that third-party vendors and partners also adhere to strict Cyber Security practices, especially when they have access to your systems.
e) Diversified Backup Solutions: Use a combination of on-site and off-site backup solutions to ensure redundancy and availability of data in case of a cyber incident.
f) Regular Backup Schedule: Establish and maintain a regular backup schedule, ensuring that all critical data is backed up at frequent intervals.
Challenges in Implementing Cyber Resilience
Some challenges in implementing Cyber Resilience include:

a) Resource Allocation: Allocating enough resources for Cyber Security initiatives is often challenging due to budget constraints. It requires a strategic approach to justify the investment and demonstrate the long-term benefits of robust cyber defences.
b) Evolving Threats: Cyber threats are dynamic, with new vulnerabilities emerging as technology advances. Organisations must remain vigilant and update their Cyber Security measures regularly to counteract these evolving threats.
c) Compliance: Keeping up with the numerous regulations and standards in the Cyber Resilience Act can be challenging. Entities must have a clear understanding of the requirements and implement a Compliance Management system to ensure adherence.
d) Skill Gap: There is a major skill gap in the Cyber Security industry, with a shortage of qualified professionals to fill the roles. Organisations need to invest in training and development to build a skilled Cyber Security workforce or outsource to specialised service providers.
Develop a future-proof network protection mindset with our Introduction to System and Network Security Training- Join now!
Entities Affected by the Cyber Resilience Act
The Act affects a wide range of entities, including:
a) Government Agencies: They must protect sensitive citizen data.
b) Businesses: From small startups to large corporations, all must secure their digital assets.
c) Healthcare Providers: They must safeguard patient information.
What are the Three Critical Component of Cyber Resilience?
Cyber resilience begins with risk mitigation, identifying, assessing, and reducing potential threats. This involves strong preventive measures, regular system updates, and employee cybersecurity training to lower the chances of an attack.
Effective incident response ensures quick detection, containment, and recovery from cyberattacks, minimising damage and maintaining stakeholder trust. Business continuity plans, including backups and alternate workflows, keep essential services running during disruptions.
What is the Cyber Resilience Act for Dummies?
It is a new EU regulation aimed at improving the cybersecurity of products with digital elements, such as software and connected devices. It ensures that these products meet essential security requirements before entering the market and throughout their lifecycle.
Designed for both consumers and businesses, the Act applies to manufacturers, importers, and distributors of digital products, including everything from smartphones and smartwatches to software like antivirus tools and photo editors. It mandates built-in security by design, transparency around vulnerabilities, and clear responsibilities for managing cyber risks.
Conclusion
The Cyber Resilience Act is a vital move towards creating a safer digital world. By grasping and putting into action the Act’s rules, organisations can greatly improve their defences against cyber threats. This ensures not only their own safety but also secures the digital future for everyone.
Prepare to tackle complex fraud cases with our Fraud Analytics Training- Sign up today!
Frequently Asked Questions
What is the Key Focus of the Cyber Resilience Act?

It focuses on strengthening cybersecurity by ensuring digital products meet strict security standards, helping organisations defend against threats, manage vulnerabilities, and recover from cyber-attacks effectively, and promoting safer digital environments across the EU.
To Whom Does the Cyber Resilience Act Apply?

It applies to a wide range of entities, including government agencies, businesses, and organisations that handle sensitive information. It aims to ensure that these entities are taking steps to safeguard themselves against cyber threats.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is the Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including the Fraud Analytics Training, Cyber Security Awareness Course, and Digital Forensics Training . These courses cater to different skill levels, providing comprehensive insights into Cyber Resilience vs Cyber Security.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Resilience, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your cyber security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 DVMS NISTCSF – Foundation Course
DVMS NISTCSF – Foundation Course
Thu 11th Jun 2026
Thu 20th Aug 2026
Thu 8th Oct 2026





 Top Rated Course
Top Rated Course




 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


